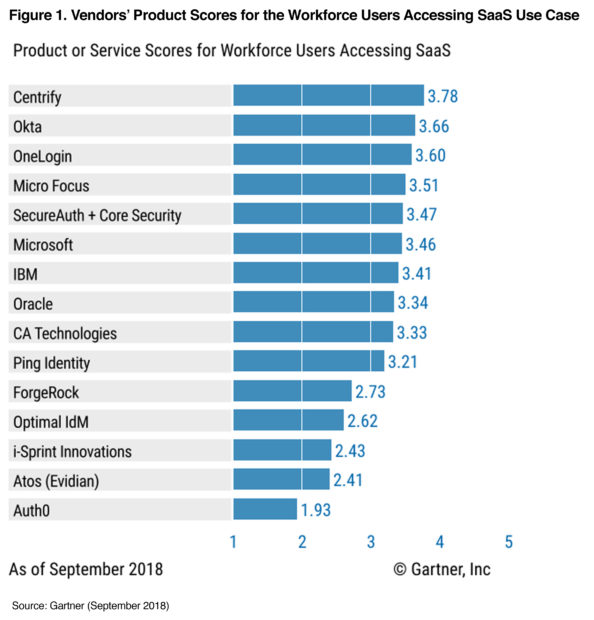
Centrify Scores Highest for Both “Workforce Users Accessing SaaS” and “Business-to-Business” in New Gartner Report
Gartner just released their first ever “Critical Capabilities for Access Management, Worldwide, 2018” report, and we are proud to see that Centrify has scored the highest of any vendor in 2 out of 3 Use Cases including “Workforce Users Accessing SaaS” (3.78 out of 5.0) and “Business-to-Business” (3.52 out of 5.0). Gartner evaluated 15 vendors’ services on nine critical...
Taking Stock: The Internet of Things, and Machine Learning Algorithms at War
It’s in the news every day; hackers targeting banks, hospitals, or, as we’ve come to fear the most, elections.
Suffice to say then that cybersecurity has, in the last few years, gone from a relatively obscure industry – let’s qualify that: not in the sense of importance, but rather how folks have been interacting with it – to one at...
Mastering Container Security: Docker, Kubernetes and More
Mastering Container Security: Docker, Kubernetes and More #outlook a{ padding:0; } body{ width:100% !important; } .ReadMsgBody{ width:100%; } .ExternalClass{ width:100%; } body{ -webkit-text-size-adjust:none; } body{ margin:0; padding:0; } img{ border:0; height:auto; line-height:100%; outline:none; text-decoration:none; } table td{ border-collapse:collapse; } #backgroundTable{ height:100% !important; margin:0; padding:0; width:100% !important; }...
LuckyMouse signs malicious NDISProxy driver with certificate of Chinese IT company
What happened?
Since March 2018 we have discovered several infections where a previously unknown Trojan was injected into the lsass.exe system process memory. These implants were injected by the digitally signed 32- and 64-bit network filtering driver NDISProxy. Interestingly, this driver is signed with a digital certificate that belongs to Chinese company LeagSoft, a developer of information security software based...
Threat Landscape for Industrial Automation Systems in H1 2018
For many years, Kaspersky Lab experts have been uncovering and researching cyberthreats that target a variety of information systems – those of commercial and government organizations, banks, telecoms operators, industrial enterprises, and individual users. In this report, Kaspersky Lab Industrial Control Systems Cyber Emergency Response Team (Kaspersky Lab ICS CERT) publishes the findings of its research on the threat...
Imperva Recognized as a 2018 Gartner Magic Quadrant WAF Leader, Five Years Running
Gartner has named Imperva as a Leader in the 2018 Gartner Magic Quadrant for Web Application Firewalls (WAF) — for the fifth year in a row!
Our combination of on-premises appliances, cloud WAF, shared threat intelligence and flexible licensing once again cement us as the best choice for companies to protect their websites and applications.
Having recently added attack analytics...
Tripwire FIM for Comprehensive Integrity Management
Tripwire FIM for Comprehensive Integrity Management #outlook a{ padding:0; } body{ width:100% !important; } .ReadMsgBody{ width:100%; } .ExternalClass{ width:100%; } body{ -webkit-text-size-adjust:none; } body{ margin:0; padding:0; } img{ border:0; height:auto; line-height:100%; outline:none; text-decoration:none; } table td{ border-collapse:collapse; } #backgroundTable{ height:100% !important; margin:0; padding:0; width:100% !important; } body,#backgroundTable{...
We know what your kids did this summer
For many kids and teenagers, summer is all about ditching school books in favor of hobbies and fun. Every year we release a report on children’s interests, as reflected in their online activity. This summer, we investigated what they prefer in their free time.
The Parental Control module in Kaspersky Lab products protects children from unwanted content, as does the...
What are botnets downloading?
Spam mailshots with links to malware and bots downloading other malware are just a couple of botnet deployment scenarios. The choice of infectious payload is limited only by the imagination of the botnet operator or customer. It might be a ransomware, a banker, a miner, a backdoor, the list goes on, and you don’t need to go far for...