KoffeyMaker: notebook vs. ATM
Despite CCTV and the risk of being caught by security staff, attacks on ATMs using a direct connection — so-called black box attacks —...
How to Operationalize the Zero Trust Security Pillar ‘Limit Access & Privilege’ with ServiceNow
An easy way for a cyber-attacker to gain access to sensitive data is by compromising an end user’s identity and credentials. Things get even...
The Rotexy mobile Trojan – banker and ransomware
On the back of a surge in Trojan activity, we decided to carry out an in-depth analysis and track the evolution of some other...
IT threat evolution Q1 2019. Statistics
These statistics are based on detection verdicts of Kaspersky Lab products received from users who consented to provide statistical data.
Quarterly figures
According to Kaspersky Security...
Centrify Launches Zero Trust Security Network Ecosystem
The world has changed. I’m not sure if it was the HBO breach, Equifax, Yahoo, or one of the many breaches since, but after...
Centrify Achieves FedRAMP Authorization
Centrify received exciting news this week that we are now FedRAMP Authorized!
For those who don’t know about FedRAMP, it is a government-wide program that...
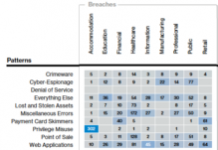
Insights from the Verizon 2018 Data Breach Investigation Report
The 2018 Verizon Data Breach Investigation Report (DBIR) was published in early April, reporting on 53,308 security incidents and 2,216 data breaches from 67...
The return of Fantomas, or how we deciphered Cryakl
In early February this year, Belgian police seized the C&C servers of the infamous Cryakl cryptor. Soon afterwards, they handed over the private keys...
KLAS Findings on Healthcare DLP Strategies
KLAS Findings on Healthcare DLP Strategies
This webinar was recorded on December 19, 2017.
- Read more