What is New with Ansible 2.8?
Read more
Nhash: petty pranks with big finances
According to our data, cryptocurrency miners are rapidly gaining in popularity. In an earlier publication we noted that cybercriminals were making use of social...
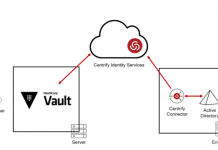
Introducing Centrify Identity Services for HashiCorp Vault
Today, Centrify is proud to announce the integration of the Centrify Identity Service with HashiCorp Vault for role-based user authentication and access to the...
Minimizing Exposure to Ransomware Attacks with Centrify Zero Trust Privilege
Ransomware attacks like the ones that wreaked havoc in Baltimore, Maryland, Albany, New York, and Genesee County, Michigan are dominating the headlines in 2019....
The 2019 DBIR is out
Once again, we are happy to support a large, voluntary, collaborative effort like the 2019 Data Breach Investigations Report. While our data contribution is...
Pocket cryptofarms
In recent months, the topic of cryptocurrency has been a permanent news fixture — the value of digital money has been see-sawing spectacularly. Such...
Roaming Mantis, part IV
One year has passed since we published the first blogpost about the Roaming Mantis campaign on securelist.com, and this February we detected new activities...
Threat Landscape for Industrial Automation Systems in H2 2018
H2 2018 in figures
All statistical data used in this report was collected using the Kaspersky Security Network (KSN), a distributed antivirus network. The data...