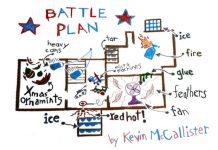
Zero Trust Lessons from a Holiday Classic
Every year when the holidays roll around, I’m amazed at the way shopping deals dominate the headlines. Black Friday and Cyber Monday are annual...
Achieve CIS Benchmarks for Cloud, Container and DevOps Environments
Achieve CIS Benchmarks for Cloud, Container and DevOps Environments #outlook a{ padding:0;...
GUEST BLOG: A Gen Z’s Perspective on Cybersecurity
I had the pleasure to mentor a summer intern named Min Ji Kim, who is returning to NYU to continue her education next week....
Hello! My name is Dtrack
Our investigation into the Dtrack RAT actually began with a different activity. In the late summer of 2018, we discovered ATMDtrack, a piece of...
Jumpstarting Your Cyberdefense Machine with CIS Controls V7
Jumpstarting Your Cyberdefense Machine with CIS Controls V7 #outlook a{ padding:0; }...
Kaspersky Security Bulletin. Overall statistics for 2017
All the statistics used in this report were obtained using Kaspersky Security Network (KSN), a distributed antivirus network that works with various anti-malware protection components....
How to Migrate to the Cloud Without Compromising Your Security Posture
How to Migrate to the Cloud Without Compromising Your Security Posture #outlook...
Financial threats in H1 2019
Introduction and methodology
Financial cyberthreats are malicious programs that attack users of online banking services, electronic money, cryptocurrency and other similar services, as well as...
Centrify Achieves FedRAMP Authorization
Centrify received exciting news this week that we are now FedRAMP Authorized!
For those who don’t know about FedRAMP, it is a government-wide program that...