Industrial Cybersecurity from Tripwire Enterprise
Industrial Cybersecurity from Tripwire Enterprise #outlook a{ padding:0; } body{ width:100% !important;...
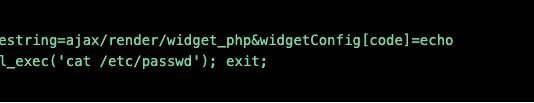
52% of Companies Don’t have a Password Vault for Privileged Access – Here’s Your...
Over the first half of 2019, Centrify issued two research reports about the adoption of Privileged Access Management (PAM) solutions and the maturity of...
Enabling Faster DDoS Mitigation for Cloud Assets
The cloud journey was considered a visionary approach less than a decade ago. Today, more than half of organizations rely on a cloud provider,...
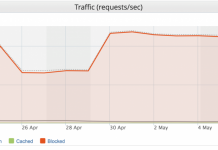
Imperva Blocks Our Largest DDoS L7/Brute Force Attack Ever (Peaking at 292,000 RPS)
Imagine you’re a developer building a new web application. You’ve followed all of the security best practices, hired a reputable penetration testing company before...
New 3-Second DDoS Mitigation SLA is 3x Faster and the Industry’s Best
Back in 2018, we made waves with a groundbreaking DDoS Mitigation SLA (service level agreement) for our DDoS Protection service that guaranteed to mitigate...
Medical Device Cybersecurity
Medical Device Cybersecurity #outlook a{ padding:0; } body{ width:100% !important; } .ReadMsgBody{...
How to steal a million (of your data)
Any user data — from passwords for entertainment services to electronic copies of documents — is highly prized by intruders. The reason is simply...
How Account Takeover Botnets Outsmart Traditional Security Controls
Account Takeover (ATO) describes when an online account is accessed and/ or used by someone other than its legitimate owner, usually for malicious purposes....
On the IoT road: perks, benefits and security of moving smartly
Kaspersky has repeatedly investigated security issues related to IoT technologies (for instance, here, or here). Earlier this year our experts have even gained foothold...
Subscriptions Are All Around Us
Read more