Centrify and SailPoint Join Forces to Apply Zero Trust Security Best Practices to Identity...
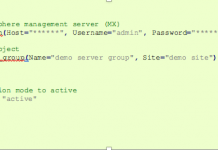
Today, Centrify is proud to announce the integration of the Centrify Privileged Access Service with SailPoint® Technologies IdentityIQ solution.
This integration provides joint customers with...
IT threat evolution Q1 2018. Statistics
Q1 figures
According to KSN:
Kaspersky Lab solutions blocked 796,806,112 attacks launched from online resources located in 194 countries across the globe.
282,807,433 unique URLs were...
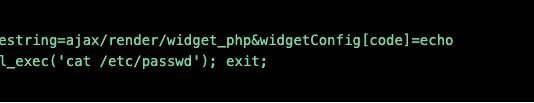
Imperva Python SDK – We’re All Consenting SecOps Here
Managing your WAF can be a complicated task. Custom policies, signatures, application profiles, gateway plugins… there’s a good reason ours is considered the best...
OPC UA security analysis
This paper discusses our project that involved searching for vulnerabilities in implementations of the OPC UA protocol. In publishing this material, we hope to...
Want to See What A Live DDoS Attack Looks Like?
We’re fortunate enough to have had Andy Shoemaker, founder of NimbusDDoS, and our own Ofer Gayer chat about DDoS attacks and shed some light on...
Jumpstarting Your Cyberdefense Machine with CIS Controls V7
Jumpstarting Your Cyberdefense Machine with CIS Controls V7 #outlook a{ padding:0; }...
How to Operationalize the Zero Trust Security Pillar ‘Limit Access & Privilege’ with ServiceNow
An easy way for a cyber-attacker to gain access to sensitive data is by compromising an end user’s identity and credentials. Things get even...
Gartner Security & Risk Management Summit 2018
Gartner Security & Risk Management Summit 2018
June 4th – 7th | National Harbor, MD
- Read more
SynAck targeted ransomware uses the Doppelgänging technique
The Process Doppelgänging technique was first presented in December 2017 at the BlackHat conference. Since the presentation several threat actors have started using this...