[R1] Tenable Identity Exposure Version 3.77.14 Fixes Multiple Vulnerabilities
Tenable Identity Exposure Version 3.77.14 Fixes Multiple Vulnerabilities Arnie Cabral Mon, 11/03/2025 - 09:50
Tenable Identity Exposure leverages third-party software to help provide underlying functionality. Several of the third-party components (.NET, SQL and curl) were found to contain vulnerabilities, and updated versions have been made available by the providers.Out of caution and in line with best practice, Tenable...
WordPress – Ultimate Dashboard exposed API Key
WordPress - Ultimate Dashboard exposed API Key Ultimate Dashboard allows to replace the default WordPress dashboard widgets with your own and give the WordPress dashboard a more meaningful use.Since at least version 3.8.3 an exposed MailerLite API key has existed allowing an attacker to interact with the MailerLite API, which could potentially lead to spam, phishing attacks, or other...
Knee-jerk corporate responses to data leaks protect brands like Qantas — but consumers are getting screwed
When courts ban people from accessing leaked data – as happened after the airline’s data breach – only hackers and scammers winFollow our Australia news live blog for latest updatesGet our breaking news email, free app or daily news podcastIt’s become the playbook for big Australian companies that have customer data stolen in a cyber-attack: call in the lawyers...
Datadog threat roundup: Top insights for Q3 2025
Threat insights from Datadog Security Labs for Q3 2025. - Read more
Learnings from recent npm supply chain compromises
A look at recent npm supply chain compromises and how we can learn from them to better prepare for future incidents. - Read more
Dell Storage Manager Multiple Vulnerabilities
Dell Storage Manager Multiple Vulnerabilities CVE-2025-43995: Authentication Bypass in DSM Data Collector (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) An unauthenticated remote attacker can access APIs exposed by ApiProxy.war in DataCollectorEar.ear by using a special SessionKey and UserId. It's been observed that the ApiSession identified by an integer key of 1 seems to be present in the "sessionHash" regardless of whether any user is currently or was...
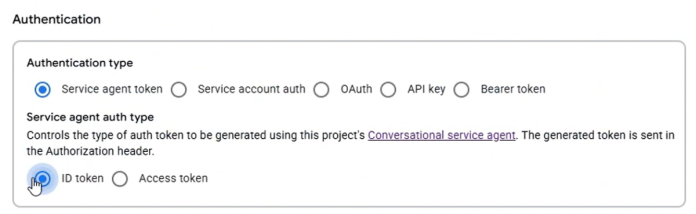
Google Cloud Platform (GCP) Dialogflow Service Agent Token Leak and Abuse Through Conversational Agents
Google Cloud Platform (GCP) Dialogflow Service Agent Token Leak and Abuse Through Conversational Agents Tenable Research has identified and responsibly disclosed a critical privilege escalation vulnerability in Google Dialogflow. This flaw allowed an attacker with access to a Dialogflow agent to take over the Dialogflow service agent and assume its privileged permissions. This vulnerability stems from a misconfiguration in how...
CoPhish: Using Microsoft Copilot Studio as a wrapper for OAuth phishing
Copilot Studio links look benign, but they can host content to redirect users to arbitrary URLs. In this post, we document a method by which a Copilot Studio agent's login settings can redirect a user to any URL, including an OAuth consent attack. - Read more
[R1] Tenable Identity Exposure Version 3.93.4 Fixes Multiple Vulnerabilities
Tenable Identity Exposure Version 3.93.4 Fixes Multiple Vulnerabilities Arnie Cabral Fri, 10/17/2025 - 10:02
Tenable Identity Exposure leverages third-party software to help provide underlying functionality. One of the third-party components (.NET) was found to contain vulnerabilities, and updated versions have been made available by the providers.Out of caution and in line with best practice, Tenable has opted to...
Capita fined £14m for data protection failings in 2023 cyber-attack
Hackers stole personal information of 6.6m people but outsourcing firm did not shut device targeted for 58 hoursThe outsourcing company Capita has been fined £14m for data protection failings after hackers stole the personal information of 6.6 million people, including staff details and those of its clients’ customers.John Edwards, the UK information commissioner who levied the fine, said the...