When the Digital World Turns Physical: The Expanding Role of Threat Intelligence in Executive Protection
Key Takeaways Cyber and physical risks are converging. Online exposure now translates into real-world danger as doxxing, deepfakes, and business email compromise blur the boundary between the virtual and physical worlds. Executives are prime targets. Their digital footprints, public visibility, and access to sensitive assets make them especially attractive to adversaries. Threat...
KinoKong – 817,808 breached accounts
In March 2021, the Russian online streaming service KinoKong suffered a data breach that was later redistributed as part of a larger corpus of data. The breach exposed over 800k unique email addresses along with names, usernames, IP addresses and MD5 password hashes. - Read more
HashJack Attack Targets AI Browsers and Agentic AI Systems
A new wave of client-side attacks bypasses enterprise defenses. - Read more
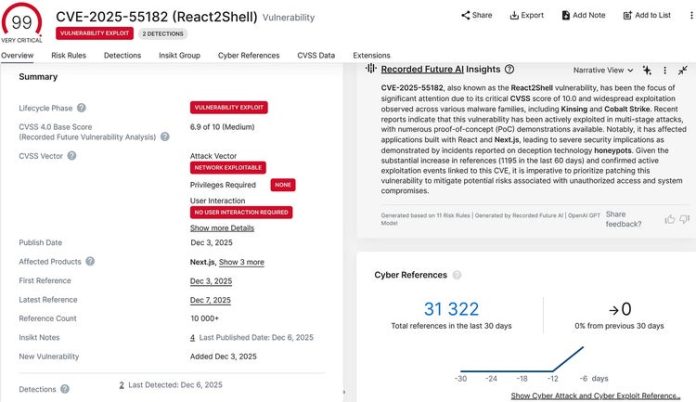
React2Shell Remote Code Execution
React2Shell is a critical unauthenticated remote code execution (RCE) vulnerability affecting React Server Components (RSC) and frameworks that implement the Flight protocol, including specific vulnerable versions of Next.js. A remote attacker can craft a malicious RSC request that triggers server-side deserialization, leading to arbitrary code execution without authentication or user interaction. - Read more
Oracle Identity Manager Pre-Auth RCE
What is the Vulnerability? CVE-2025-61757 is a critical pre-authentication remote code execution vulnerability in Oracle Identity Manager’s REST WebServices. This vulnerability allows an unauthenticated attacker to exploit URI and matrix parameter parsing weaknesses to bypass authentication and execute arbitrary code over HTTP. Successful exploitation...
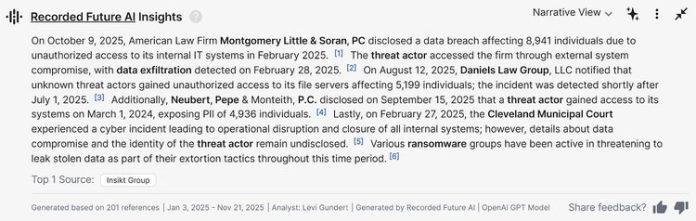
The Hidden Cascade: Why Law Firm Breaches Destroy More than Data
In the wake of the Salesforce/Gainsight breach (kudos to Salesforce for transparently sharing indicators of compromise and updated progress on remediation), third-party cyber and exposure risk is top of mind for many CISOs. Professional services firms are often overlooked in this context, with disastrous consequences. Law firms, specifically, are particularly vulnerable to creating downstream risk impacts given the...
The Bug That Won’t Die: 10 Years of the Same Mistake
CVE-2025-55182 Intelligence Card c/o Recorded Future There are now multiple publicly available exploit scripts (I forked one on GitHub here) for the React and Next.js vulnerabilities (CVE-2025-55182 and CVE-2025-66478). The underlying issue is data serialization/deserialization, which evoked thoughts about a blog I wrote in 2016, addressing the same issue...
Imperva Customers Protected Against React Server Components (RSC) Vulnerability
Overview
On December 3, 2025, the React and Next.js teams disclosed a critical security vulnerability (CVSS 10.0), identified as React2Shell, affecting applications that leverage React Server Components together with Server Actions or Server Functions.
The React2Shell vulnerability stems from improper validation of client-supplied data within certain server-side React features. An unauthenticated attacker could exploit this flaw by sending specially crafted requests,...
2026 Phishing Threat Predictions: 5 Key Takeaways
As organizations prepare for another year of highly sophisticated, AI-driven email threats, Cofense’s 2026 Phishing Threat Predictions webinar brought together experts Joshua Bartolomie, Max Gannon, and Chance Caldwell to break down what security teams should anticipate in the year ahead. Their insights reveal a threat landscape shaped by accelerating offensive and defensive AI adoption and the growing need for...
CVE-2025-55182 (React2Shell): Remote code execution in React Server Components and Next.js
Learn more about the CVE-2025-55182 vulnerability affecting React Server Components and affecting Next.js. - Read more