Broken access control on API endpoints
CVSSv3 Score: 6.2
An Improper access control vulnerability in FortiSOAR may allow Information disclosure to an authenticated attacker via crafted requests
Revised on 2025-12-09 00:00:00
- Read more
Private key readable by admin
CVSSv3 Score: 5.9
A key management error vulnerability in FortiManager, FortiAnalyzer and FortiPortal may allow an authenticated admin to retrieve a certificate's private key via the device's admin shell.
Revised on 2025-12-10 00:00:00
- Read more
Cofense Delivers Faster, Smarter Phishing Defense with New Capabilities
LEESBURG, Va., December 9, 2025 - Cofense, the leader in intelligence-driven phishing defense, today announced significant advancements across its portfolio, introducing Smart Reinforcement within its Security Awareness Training solution, and unveiling the latest release of Triage 1.30 within its Phishing Detection and Response (PDR) solution. These enhancements mark a major step forward in Cofense’s mission to deliver faster, smarter, and...
Phishers Get Creative: The NoteGPT Twist You Didn’t See Coming
By: Hendrix Garcia, Cofense Phishing Defense CenterNoteGPT is an AI-generated tool that converts lengthy lectures, meetings, or videos into concise, easy-to-read notes in just seconds. While seemingly useful, threat actors are now exploiting it to host fake files and lure victims. They upload malicious content to NoteGPT, then share what appears to be a harmless “document” or “note”. Because...
5 Real-Word Third-Party Risk Examples
Key Takeaways Static vendor checks fall short: Traditional, point-in-time third-party risk management practices (e.g. annual questionnaires) leave organizations blind to emerging vendor threats between audits. Continuous monitoring is now a must. Five common risk scenarios: Supply chain attacks, widespread software vulnerabilities, hidden fourth-party dependencies, vendor credential theft, and vendor instability each illustrate how “trusting” vendors can lead...
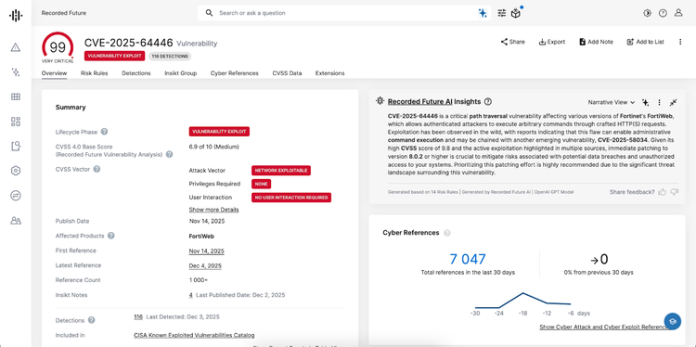
November 2025 CVE Landscape: 10 Critical Vulnerabilities Show 69% Drop from October
November 2025 saw a significant 69% decrease in high-impact vulnerabilities, with Recorded Future's Insikt Group® identifying 10 vulnerabilities requiring immediate attention, down from 32 in October. What security teams need to know: Fortinet leads concerns: Two critical FortiWeb vulnerabilities (CVE-2025-64446 and CVE-2025-58034) are under active exploitation LANDFALL spyware campaign: Threat actors weaponized Samsung's image processing flaw (CVE-2025-21042)...
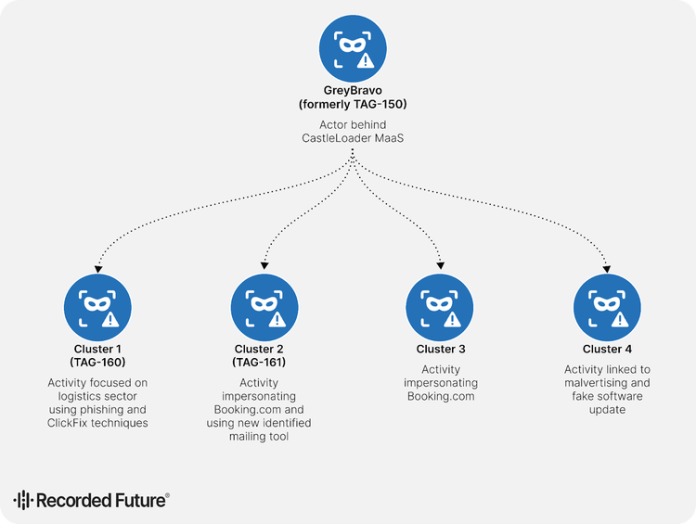
GrayBravo’s CastleLoader Activity Clusters Target Multiple Industries
Note: The analysis cut-off date for this report was November 10, 2025 Executive Summary Insikt Group continues to monitor GrayBravo (formerly tracked as TAG-150), a technically sophisticated and rapidly evolving threat actor first identified in September 2025. GrayBravo demonstrates strong adaptability, responsiveness to public exposure, and operates a large-scale, multi-layered infrastructure. Recent analysis of GrayBravo’s ecosystem uncovered four...
10 Years of Let’s Encrypt Certificates
On September 14, 2015, our first publicly-trusted certificate went live. We were proud that we had issued a certificate that a significant majority of clients could accept, and had done it using automated software. Of course, in retrospect this was just the first of billions of certificates. Today, Let’s Encrypt is the largest certificate authority in the world in...
ShellShock Makes a Comeback and RondoDox Changes Tactics
Legacy bugs continue to serve attackers. - Read more
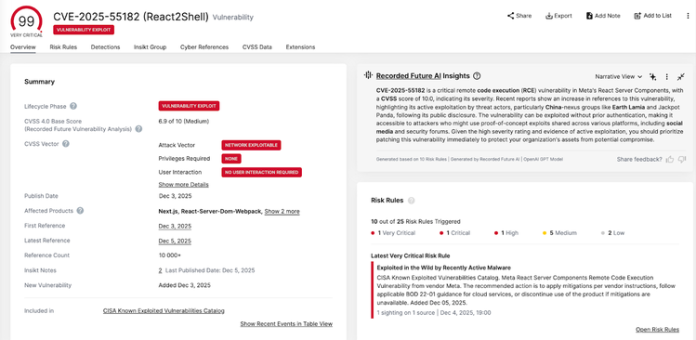
Critical React2Shell Vulnerability Under Active Exploitation by Chinese Threat Actors
Last updated on 9 December. A critical vulnerability in React Server Components is allegedly being actively exploited by multiple Chinese threat actors, Recorded Future recommends organizations patch their systems immediately. What's Happening CVE-2025-55182, dubbed "React2Shell," affects React Server Components versions 19.0, 19.1.0, 19.1.1, and 19.2.0 in several Meta packages. Amazon's AWS Threat Intelligence team reported on December 4...