CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
The purpose of this Alert is to provide resources for organizations with Cisco Software-Defined Wide-Area Networking (SD-WAN) systems, including Federal Civilian Executive Branch (FCEB) agencies, to address ongoing exploitation of multiple vulnerabilities. Notably, the Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-20127 and CVE-2022-20775 to its Known Exploited Vulnerabilities (KEV) Catalog on Feb. 25, 2026. As a result of the...
Microsoft warns of job‑themed repo lures targeting developers with multi‑stage backdoors
Microsoft says it has uncovered a coordinated campaign targeting software developers through malicious repositories posing as legitimate Next.js projects and technical assessments. The campaign employs carefully crafted lures to blend into routine workflows, such as cloning repositories, opening projects, and running builds, thereby allowing the malicious code to execute undetected. Telemetry collected during an incident...
Canadian Tire – 38,306,562 breached accounts
In October 2025, retailer Canadian Tire was the victim of a data breach that exposed almost 42M records. The data contained 38M unique email addresses along with names, phone numbers and physical addresses. Passwords were stored as PBKDF2 hashes and for a subset of records, dates of birth and partial credit card data were also included (card type, expiry...
Abusing Windows File Explorer and WebDAV for Malware Delivery
By: Kahng An, Intelligence TeamCofense Intelligence has been tracking how threat actors are abusing Windows File Explorer’s ability to retrieve remote files over Web-based Distributed Authoring and Versioning (WebDAV), and HTTP-based file management protocol, to trick victims into downloading malware. WebDAV is a relatively unpopular method of file transfer and remote file storage nowadays, but it is natively supported...
Elastic AutoOps is now free: Investing in our community
We're making AutoOps free for every self-managed Elasticsearch user. It analyzes your clusters, identifies what's wrong, and tells you how to fix it. It’s an investment in the open source community — no license required or infrastructure to maintain. - Read more
The Ghost in the Shell: Why Agentic AI is a Corporate Security Nightmare
Autonomous AI agents blur security boundaries, enabling data exfiltration, privilege abuse, and insider‑level risk in enterprises. - Read more
Google Alerts Users to Serious Chrome Bugs With Takeover Risk
Google released a Chrome security update patching three high-severity vulnerabilities, including memory flaws that could enable remote attacks.
The post Google Alerts Users to Serious Chrome Bugs With Takeover Risk appeared first on TechRepublic. - Read more
Cost of Insider Incidents Surges 20% to Nearly $20m
DTEX claims insider incidents cost $19.5m in 2025, with employee negligence most expensive - Read more
Multi-Tenant API Access: Centralize, Scale, and Secure Your Operations
For teams managing dozens, or even hundreds, of tenants, API access quickly becomes operational overhead. Managed Security Service Providers and large enterprises often find themselves maintaining separate credentials for every environment, adding friction to automation, reporting, and day-to-day operations.To address this, we are excited to announce multi-tenant API access, a new authentication capability designed to drive operational efficiency and...
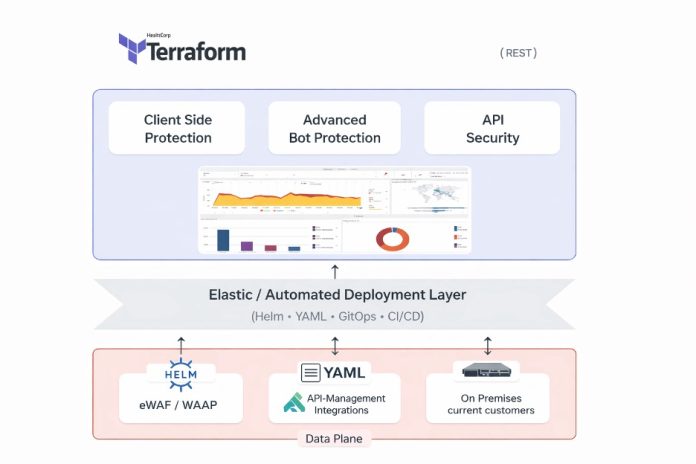
Integrating Advanced API Security with Imperva Gateway Environment
As APIs power the majority of modern web applications, implementing robust API security is no longer optional – it’s a critical necessity for data protection. This guide explores how to seamlessly integrate API gateway security into your Imperva on-premises environment to mitigate OWASP Top 10 threats, ensuring both web application and business logic threats are effectively managed.
The Need for...