Cisco ASA and FTD Firewall RCE
Critical zero-day vulnerabilities affecting Cisco Secure Firewall Adaptive Security Appliance (ASA) and Cisco Secure Firewall Threat Defense (FTD) software have been actively exploited in the wild. The campaign is widespread and involves exploiting zero-day vulnerabilities to gain unauthenticated remote code execution on ASAs, as well as manipulating read-only memory (ROM) to persist through reboot and system upgrade. This activity...
AUTOSUR – 487,226 breached accounts
In March 2025, the French vehicle inspection company AUTOSUR suffered a data breach exposing over 10M customer records, though only 487k unique email addresses were present. The compromised data included names, phone numbers, physical addresses, and vehicle details such as make and model, VIN, and registration plate. AUTOSUR later issued a disclosure notice with further details. - Read...
ArcaneDoor Attack (Cisco ASA Zero-Day)
What is the Attack? Cisco has disclosed a state-sponsored espionage campaign targeting Cisco Adaptive Security Appliances (ASA) , which are widely deployed for firewall, VPN, and security functions. Initial Advisory (April 24): Attackers exploited two previously...
The Botting Network – 96,320 breached accounts
In August 2012, the forum for making money with botting "The Botting Network" suffered a data breach that exposed 96k user records. The now defunct vBulletin forum leaked 96k email addresses, usernames, dates of birth and salted MD5 password hashes. - Read more
Web Hosting Talk – 515,149 breached accounts
In July 2016, the Web Hosting Talk forum suffered a data breach that was subsequently listed for sale. The breach of the vBulletin based forum exposed 515k user records including usernames, email addresses, IP addresses and salted MD5 password hashes. - Read more
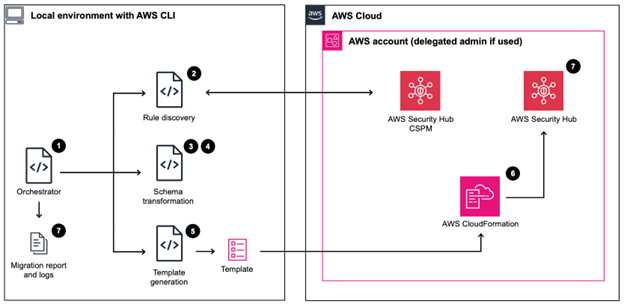
Security Hub CSPM automation rule migration to Security Hub
A new version of AWS Security Hub is now generally available with new capabilities to aggregate, correlate, and contextualize your security alerts across Amazon Web Services (AWS) accounts. The prior version is now known as AWS Security Hub CSPM and will continue to be available as a unique service focused on cloud security posture management and finding...
Libbiosig, Grassroot DiCoM, Smallstep step-ca vulnerabilities
Cisco Talos’ Vulnerability Discovery & Research team recently disclosed vulnerabilities in Biosig Project Libbiosig, Grassroot DiCoM, and Smallstep step-ca.The vulnerabilities mentioned in this blog post have been patched by their respective vendors, all in adherence to Cisco’s third-party vulnerability disclosure policy, except for Grassroot, as the DiCoM vulnerabilities are zero-days. For Snort coverage that can detect the exploitation of...
UAT-9686 actively targets Cisco Secure Email Gateway and Secure Email and Web Manager
Cisco Talos recently discovered a campaign targeting Cisco AsyncOS Software for Cisco Secure Email Gateway, formerly known as Cisco Email Security Appliance (ESA), and Cisco Secure Email and Web Manager, formerly known as Cisco Content Security Management Appliance (SMA). We assess with moderate confidence that the adversary, who we are tracking as UAT-9686, is a Chinese-nexus advanced persistent threat...
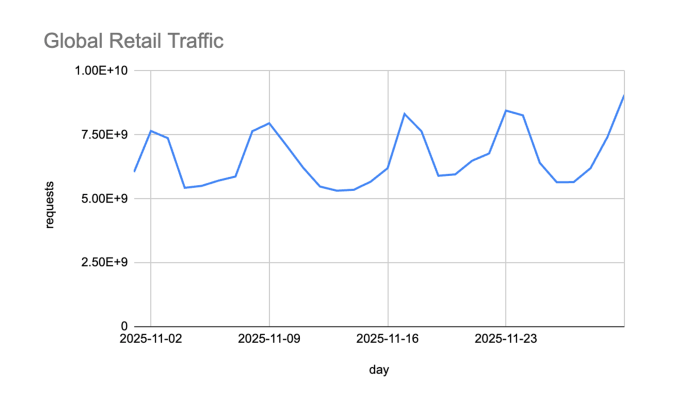
Black Friday 2025 in Review: What Retailers Need to Know About This Year’s Holiday Shopping Season
Holiday shopping season is in full swing, and Black Friday 2025 continued to demonstrate that consumer demand and attacker activity shows no signs of slowing. According to Adobe Analytics, U.S. consumers spent $11.8 billion online on Black Friday, setting a new record and highlighting sustained strength in online shopping. Yet behind this surge in legitimate traffic, retailers also faced...
GachiLoader: Defeating Node.js Malware with API Tracing
Research by: Sven Rath (@eversinc33), Jaromír Hořejší (@JaromirHorejsi) Key Points
The YouTube Ghost Network is a malware distribution network that uses compromised accounts to promote malicious videos and spread malware, such as infostealers. One of the observed campaigns uses a new, heavily obfuscated loader malware written in Node.js, which we call GachiLoader. To make it easier to analyze obfuscated Node.js malware, Check Point Research developed...