Digital Threat Detection Tools & Best Practices
Key Takeaways Intelligence drives better decisions. High-performing teams use threat intelligence not just for detection, but to inform strategic business decisions and communicate risk to leadership. Maturity means efficiency. Advanced programs focus on automation, high-fidelity indicators, and cross-functional collaboration—freeing analysts to concentrate on strategic initiatives. Information overload is the top challenge. Teams need better integrations and AI-powered...
Ni8mare and N8scape flaws among multiple critical vulnerabilities affecting n8n
OverviewOn November 18, 2025, a patched release was published for a critical unauthenticated file read vulnerability in n8n, a popular piece of automation software. The advisory for this vulnerability, CVE-2026-21858, was subsequently published on January 7, 2026; the vulnerability holds a CVSS score of 10.0. If a server has a custom configured web form that implements file uploads with...
Resolutions, shmesolutions (and what’s actually worked for me)
Welcome to this week’s edition of the Threat Source newsletter. I went to bed at 8:30 p.m. on New Year’s Eve, and I think that’s pretty indicative of how I approach the whole idea of New Year’s resolutions. I love to count down to the new year with loved ones as much as the next person, but I have really conflicted feelings about traditional resolutions. On one hand, it’s great...
GoBruteforcer Botnet Targets Linux Servers
The GoBruteforcer botnet has been observed targeting exposed Linux servers on services like FTP and MySQL - Read more
What tools help reduce fraud or friendly fraud for online businesses?
A customer buys. You ship. Everyone seems happy. Then, a few weeks later, you get a chargeback. Or you notice the same card being tried again and again in a few seconds, failing at first and then working. It can be a sign someone is trying to steal card info to see what goes through. That’s the part most...
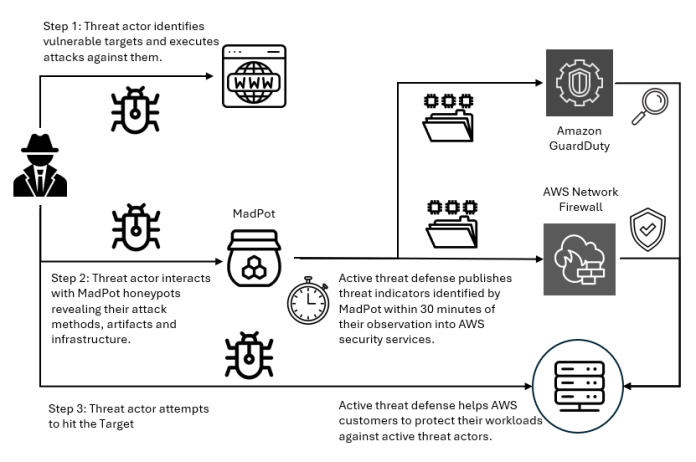
Real-time malware defense: Leveraging AWS Network Firewall active threat defense
Cyber threats are evolving faster than traditional security defense can respond; workloads with potential security issues are discovered by threat actors within 90 seconds, with exploitation attempts beginning within 3 minutes. Threat actors are quickly evolving their attack methodologies, resulting in new malware variants, exploit techniques, and evasion tactics. They also rotate their infrastructure—IP addresses, domains, and URLs. Effectively...
Cybersecurity at the edge: Securing rugged IoT in mission-critical environments
Edge computing is no longer a futuristic concept; it’s a reality shaping mission-critical operations across defense, utilities and public safety. Rugged IoT devices, engineered to withstand extreme conditions, are the backbone of this transformation. They enable real-time decision-making in environments where traditional IT infrastructure cannot survive. But this progress comes with risk. These devices often...
CVE-2024-43899 drm/amd/display: Fix null pointer deref in dcn20_resource.c
Information published. - Read more
CVE-2024-43901 drm/amd/display: Fix NULL pointer dereference for DTN log in DCN401
Information published. - Read more
Hitachi Energy Asset Suite
View CSAF
Summary
Hitachi Energy is aware of a Jasper Report vulnerability that affects the Asset Suite product versions mentioned in this document below. This vulnerability can be exploited to carry out remote code execution (RCE) attack on the product. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation.
The following versions of Hitachi Energy Asset Suite are affected:
Asset...