CVE-2026-23229 crypto: virtio – Add spinlock protection with virtqueue notification
Information published. - Read more
Elastic Stack 9.3.1 released
Version 9.3.1 of the Elastic Stack was released today. We recommend you upgrade to this latest version. We recommend 9.3.1 over the previous versions 9.3.0
The 9.3.1 release contains fixes for potential security vulnerabilities. Please see our security advisory for more details.
For details of the issues that have been fixed and a full list of changes for each product in...
Recorded Future Expands Coverage of Scams and Financial Fraud with Money Mule Intelligence from CYBERA
Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifying data on scam-linked bank accounts. Available for purchase now via the Recorded Future Platform, Money Mule Intelligence helps fraud teams identify the accounts criminals use to extract and move stolen funds—addressing a critical gap as scams increasingly...
Critical Cisco Catalyst Vulnerability Exploited in the wild (CVE-2026-20127)
OverviewOn February 25, 2026, Cisco disclosed a critical authentication bypass vulnerability in Cisco Catalyst SD‑WAN Controller and Cisco Catalyst SD‑WAN Manager, tracked as CVE‑2026‑20127, that allows an unauthenticated attacker to gain administrative access to affected systems. The Cisco Catalyst SD-WAN Controller and Manager are core components of Cisco’s software-defined wide area networking (SD-WAN) architecture. The issue was originally identified...
Google Cloud Platform (GCP) Vertex AI Workbench Cross-Tenant Full Account Takeover with Managed End User Credentials
Google Cloud Platform (GCP) Vertex AI Workbench Cross-Tenant Full Account Takeover with Managed End User Credentials Tenable Research has identified and responsibly disclosed a critical vulnerability in Google Vertex AI Workbench. This flaw enabled a cross-tenant Full Account Takeover by exfiltrating the managed End User Credentials (EUC) of any GCP user with minimal interaction.The vulnerability exploits the Single User...
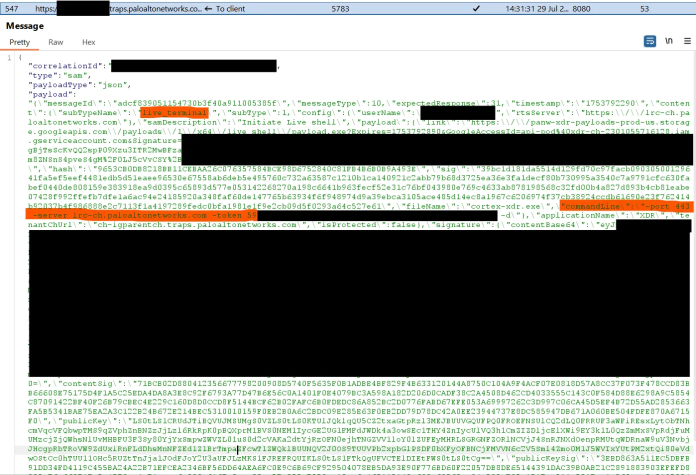
Hackers Can Abuse Cortex XDR Live Terminal Feature for C2 Communications
A newly disclosed research finding has revealed that Palo Alto Networks’ Cortex XDR Live Terminal feature can be turned into a command-and-control (C2) channel by attackers. Since this feature runs inside a trusted endpoint detection and response (EDR) agent, the traffic it produces is largely accepted by enterprise security tools, making this a quiet and difficult-to-detect abuse method....
Active exploitation of Cisco Catalyst SD-WAN by UAT-8616
Cisco Talos is tracking the active exploitation of CVE-2026-20127, a vulnerability in Cisco Catalyst SD-WAN Controller, formerly vSmart, that allows an unauthenticated remote attacker to bypass authentication and obtain administrative privileges on the affected system by sending a crafted request to an affected system. Successful exploitation may allow the attacker to gain administrative privileges on the Controller as an...
Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852
By Aviv Donenfeld and Oded Vanunu Executive Summary Check Point Research has discovered critical vulnerabilities in Anthropic’s Claude Code that allow attackers to achieve remote code execution and steal API credentials through malicious project configurations. The vulnerabilities exploit various configuration mechanisms including Hooks, Model Context Protocol (MCP) servers, and environment variables -executing arbitrary shell commands and exfiltrating Anthropic API...
Cisco Catalyst SD-WAN users targeted in series of cyber attacks
The NCSC, Cisa, and other Five Eyes agencies have warned of mass exploitation of vulnerabilities in Cisco Catalyst SD-WAN, which Cisco is attributing to an unknown threat actor called UAT-8616. - Read more