Microsoft DCU uses UK courts to hunt down cyber criminals
Microsoft has taken down the RedDVS cyber crime-as-a-service network after obtaining a UK court order, marking its first civil legal action outside of the US - Read more
Siemens RUGGEDCOM ROS
View CSAF
Summary
Ruggedcom ROS devices contain a temporary denial of service vulnerability that could allow an attacker to crash and restart the device. Siemens has released new versions for the affected products and recommends to update to the latest versions.
The following versions of Siemens RUGGEDCOM ROS are affected:
RUGGEDCOM RMC8388 V5.X (CVE-2025-40935)
RUGGEDCOM RS416Pv2 V5.X (CVE-2025-40935)
RUGGEDCOM RS416v2 V5.X (CVE-2025-40935)
RUGGEDCOM RS900 (32M) V5.X...
Secure Connectivity Principles for Operational Technology (OT)
CISA and the UK National Cyber Security Centre (NCSC-UK), in collaboration with federal and international partners, have released Secure Connectivity Principles for Operational Technology (OT) guidance to help asset owners address increasing business and regulatory pressures for connectivity into operational technology (OT) networks.
This guidance outlines eight principles to use as a framework to design, secure, and manage connectivity into...
Brushstrokes and breaches with Terryn Valikodath
Cisco Talos is kicking off the new year with a behind-the-scenes look at incident response through the eyes of Terryn Valikodath, Senior Incident Response Consultant at Talos. In this episode, Amy sits down with Terryn to explore the realities of a job that blends technical know-how with communication skills, proactive planning, and a passion for problem-solving. Terryn’s path to...
CVE-2025-64678 Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability
Updated the build numbers. This is an informational update only. - Read more
International Threats: How Malware Campaigns Vary Across Non-English Languages
By: Max GannonCofense Intelligence relies on over 35 million trained employees from around the world. As a result, a considerable number of analyzed campaigns are written in languages other than English. This report covers from May 2023 to May 2025, providing a historical perspective that demonstrates long-term patterns and trends seen over the last several years. It focuses on...
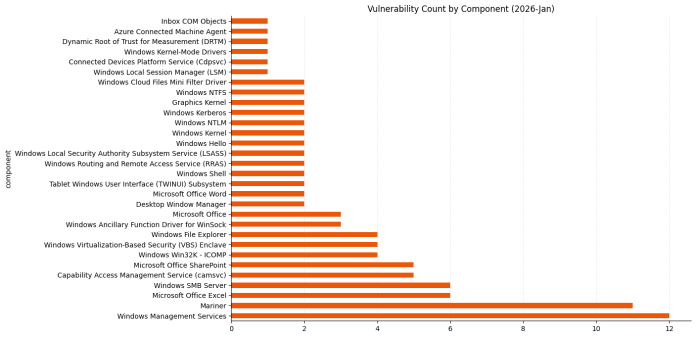
Patch Tuesday – January 2026
Microsoft is publishing 114 vulnerabilities this January 2026 Patch Tuesday. Today’s menu includes just one vulnerability marked as exploited in the wild, as well as two vulnerabilities where Microsoft is aware of public disclosure. There are no critical remote code execution or elevation of privilege vulnerabilities. So far this month, Microsoft has already provided patches to address one browser...
Unpatchable Vulnerabilities of Kubernetes: CVE-2020-8554
A look at how Kubernetes CVE-2020-8554 works - Read more
Microsoft Patch Tuesday for January 2026 — Snort rules and prominent vulnerabilities
Microsoft has released its monthly security update for January 2026, which includes 112 vulnerabilities affecting a range of products, including 8 that Microsoft marked as “critical”. In this month's release, Microsoft observed one of the included “important” vulnerabilities, CVE-2026-20805, as being exploited in the wild. Out of 8 "critical" entries, 6 are remote code execution (RCE) vulnerabilities in Microsoft Windows services and applications including Windows Local Security Authority Subsystem Service (LSASS), Microsoft Word, Microsoft Excel, and...
When AI Gets Bullied: How Agentic Attacks Are Replaying Human Social Engineering
AI Security Insights – January 2026 - Read more