Implementing data governance on AWS: Automation, tagging, and lifecycle strategy – Part 1
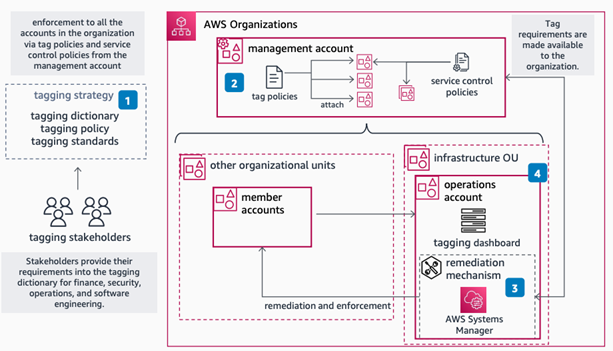
Generative AI and machine learning workloads create massive amounts of data. Organizations need data governance to manage this growth and stay compliant. While data governance isn’t a new concept, recent studies highlight a concerning gap: a Gartner study of 300 IT executives revealed that only 60% of organizations have implemented a data governance strategy, with 40% still...
Chromium: CVE-2026-0907 Incorrect security UI in Split View
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2024 ) for more information. - Read more
Cisco finally patches seven-week-old zero-day flaw in Secure Email Gateway products
Better late than never. Cisco this week patched a ‘critical’ zero-day flaw in the company’s email security and management gateways that has hung over customers’ heads since December. Tracked as CVE-2025-20393, the vulnerability affects Cisco’s AsyncOS Software running on the physical or virtual Secure Email Gateway (SEG) and Secure Email and Web Manager (SEWM) products....
Metasploit Wrap-Up 01/16/2026
Persistence, dMSA Abuse & RCE GoodiesThis week, we have received a lot of contributions from the community, such as h00die, Chocapikk and countless others, which is greatly appreciated. This week’s modules and improvements in Metasploit Framework range from new modules, such as dMSA Abuse (resulting in escalation of privilege in Windows Active Directory environments), authenticated and unauthenticated RCE modules, as well as...
Metasploit Wrap-Up 01/16/2025
Persistence, dMSA Abuse & RCE GoodiesThis week, we have received a lot of contributions from the community, such as h00die, Chocapikk and countless others, which is greatly appreciated. This week’s modules and improvements in Metasploit Framework range from new modules, such as dMSA Abuse (resulting in escalation of privilege in Windows Active Directory environments), authenticated and unauthenticated RCE modules, as well as...
Enterprise Spotlight: Setting the 2026 IT agenda
IT leaders are setting their operations strategies for 2026 with an eye toward agility, flexibility, and tangible business results. Download the January 2026 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World and learn about the trends and technologies that will drive the IT agenda in the year...
Analyzing React2Shell Threat Actors
Sensor Intel Series: December CVE-2025-55182 Trends - Read more
Go Programming Language 1.26 Patches Several Security Flaws
The patched issues span core standard library components including archive/zip and net/http, as well as security-sensitive areas of the crypto/tls stack.
The post Go Programming Language 1.26 Patches Several Security Flaws appeared first on TechRepublic. - Read more
TamperedChef Malvertising Campaign Drops Malware via Fake PDF Manuals
TamperedChef creates backdoors and steals user credentials – particularly in organizations reliant on technical equipment - Read more
Account Compromise Surged 389% in 2025, Says eSentire
An eSentire report showed credential theft accounted for 74% of all observed cyber threats in 2025 - Read more