Burner phones and lead-lined bags: a history of UK security tactics in China
Starmer’s team is wary of spies but such fears are not new – with Theresa May once warned to get dressed under a duvetWhen prime ministers travel to China, heightened security arrangements are a given – as is the quiet game of cat and mouse that takes place behind the scenes as each country tests out each other’s tradecraft...
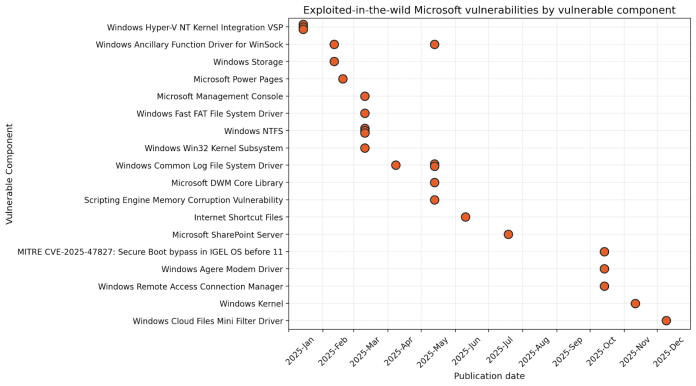
Patch Tuesday and the Enduring Challenge of Windows’ Backwards Compatibility
IntroductionIf you received an email with the subject “I LOVE YOU” and an attachment called “LOVE-LETTER-FOR-YOU.TXT”, would you open it? Probably not, but back in the year 2000, plenty of people did exactly that. The internet learned a hard lesson about the disproportionate power available to a university dropout with some VBScript skills, and millions of ordinary people suffered...
Autonomous System Uncovers Long-Standing OpenSSL Flaws
A recent update has fixed 12 vulnerabilities in OpenSSL, some existing in the codebase for years - Read more
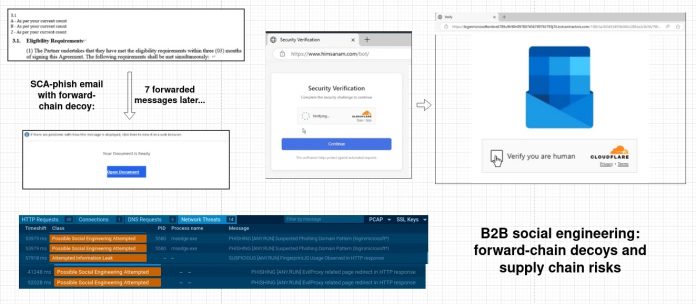
Threat Actors Leverage Real Enterprise Email Threads to Deliver Phishing Links
In a sophisticated supply chain phishing attack, threat actors hijacked an ongoing email thread among C-suite executives discussing a document awaiting final approval. The intruder, posing as a legitimate participant, replied directly with a phishing link mimicking a Microsoft authentication form. Researchers attribute this to a compromised sales manager account at an enterprise contractor, allowing seamless insertion into a...
Cyber Security Report 2026
Check Point Research continuously investigates real-world attacks, vulnerabilities, attackers’ infrastructure, and emerging techniques across global networks and environments. The Cyber Security Report 2026 consolidates our research efforts throughout 2025 to deliver a clear, data-driven view of the current threat landscape and its trajectory in 2026. As Check Point’s flagship annual research publication, the report serves as a reference point...
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard Tenable Research has identified and responsibly disclosed a data exfiltration vulnerability in Google Cloud Monitoring. This flaw allowed an attacker to leak sensitive data from a victim's BigQuery datasets by abusing the Observability Analytics widget in custom dashboards.Cloud Monitoring dashboards are executed automatically when browsing, and the...
Multiple Critical SolarWinds Web Help Desk Vulnerabilities: CVE-2025-40551, CVE-2025-40552, CVE-2025-40553, CVE-2025-40554
OverviewOn January 28, 2026, SolarWinds published an advisory for multiple new vulnerabilities affecting their Web Help Desk product. Web Help Desk is an IT help desk ticketing and asset management software solution. Of the six new CVEs disclosed in the advisory, four are critical, and allow a remote attacker to either achieve unauthenticated remote code execution (RCE) or bypass...
SmarterTools SmarterMail RCE
What is the Vulnerability? An actively targeted vulnerability has been identified in SmarterTools SmarterMail, tracked as CVE-2025-52691, with a CVSS score of 10.0 (Critical). The flaw allows unauthenticated attackers to upload arbitrary files to any location on the mail server, potentially resulting in remote code execution...
Trusted, Signed, Still Malicious. Exploiting Custom Email Text to Bypass Security Controls
By: Kahng An, Intelligence TeamA recent series of phone scam emails has been able to bypass traditional email security measures by placing malicious messages within document names, online meeting descriptions, or account name fields. These emails redirect otherwise legitimate business emails to potential victims, and are particularly notable for embedding phone scams and other malicious content while still retaining...