Zimbra Collaboration Local File Inclusion
What is the Vulnerability? A Local File Inclusion (LFI) vulnerability (CVE-2025-68645) exists in the Zimbra Collaboration Suite (ZCS) Webmail Classic UI due to improper handling of user-supplied request parameters in the RestFilter servlet. An unauthenticated remote attacker can craft malicious requests, potentially exposing sensitive configuration and...
Context engineering: The missing layer for trusted AI in financial services
AI in financial services breaks down without trusted context. Discover how context engineering enables real-time, explainable, and compliant AI and how Elastic powers fraud prevention, risk management, and digital customer experience. - Read more
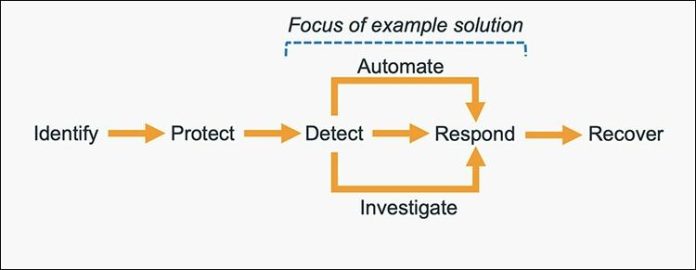
How to get started with security response automation on AWS
At AWS, we encourage you to use automation. Not just to deploy your workloads and configure services, but to also help you quickly detect and respond to security events within your AWS environments. In addition to increasing the speed of detection and response, automation also helps you scale your security operations as your workloads in AWS increase and scale...
I’m locked in!
Welcome to this week’s edition of the Threat Source newsletter.I’ve struggled a lot over the last few years with balance. I want to follow the news closely, but at the same time, I want to block everything out for self-preservation. Add in the fact that I love history and I’m an empath, and you’ve got a lovely concoction of feeling things intensely, mixed with echoes of...
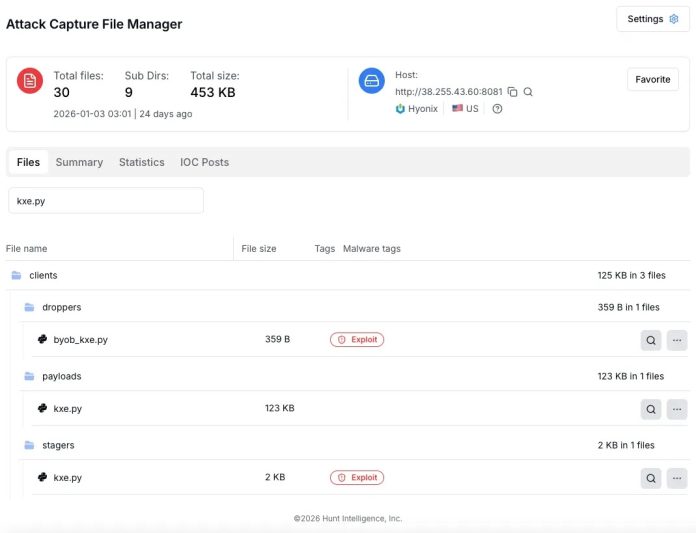
Exposed Open Directory Leaks BYOB Framework Across Windows, Linux, and macOS
Threat researchers have uncovered an actively serving command and control server hosting a complete deployment of the BYOB framework following the discovery of an exposed open directory. The server, located at IP address 382554360 on port 8081, was found distributing malicious payloads designed to establish persistent remote access across Windows, Linux, and macOS systems. Hosted by Hyonix...
Supply chain attack on eScan antivirus: detecting and remediating malicious updates
UPD 30.01.2026: Added technical details about the attack chain and more IoCs.
On January 20, a supply chain attack has occurred, with the infected software being the eScan antivirus developed by an Indian company MicroWorld Technologies. The previously unknown malware was distributed through the eScan update server. The same day, our security solutions detected and prevented cyberattacks involving this malware....
Microsoft releases update to address zero-day vulnerability in Microsoft Office
Microsoft has published three out-of-band (OOB) updates so far in January 2026. One of these updates was released to address a vulnerability, CVE-2026-21509, affecting Microsoft Office that has been reportedly exploited in the wild. Additional OOB updates have been published to resolve operational issues experienced following installation of the updates released as part of the standard Microsoft Patch Tuesday process.CVE-2026-21509 was published to address a security feature bypass vulnerability affecting...
Identitäten im Fokus von Cyberkriminellen
Cyberkriminelle haben es inzwischen vermehrt auf digitale Identitäten abgesehen.khunkornStudio – shutterstock.com Der State of Incident Response Report 2026 von Eye Security zeigt: Cyberangriffe auf Unternehmen erfolgen zunehmend unbemerkt und die Schäden entstehen innerhalb von Minuten. Demnach setzen die Angreifer inzwischen weniger darauf, Systeme zu hacken, sondern bestehende Zugänge ausnutzen. Identitätsbasierte Angriffe dominieren das Feld, wobei...
Microsoft Previews Windows 11 Update With Smarter AI and Phone Continuity
Here’s a peek at AI assistance, phone-to-PC handoff, accessibility improvements, security fixes, and stability updates.
The post Microsoft Previews Windows 11 Update With Smarter AI and Phone Continuity appeared first on TechRepublic. - Read more
RAMP ransomware forum goes dark in probable FBI sting
RAMP, an infamous Russian-speaking cyber crime forum, has gone off the air after an apparent US operation. - Read more