Siemens SINEC NMS
View CSAF
Summary
Multiple Siemens products are affected by two local privilege escalation vulnerabilities which could allow an low privileged attacker to load malicious DLLs, potentially leading to arbitrary code execution with elevated privileges. Siemens has released new versions for the affected products and recommends to update to the latest versions.
The following versions of Siemens SINEC NMS are affected:
SINEC NMS: Versions...
Ryan Liles, master of technical diplomacy
Cisco Talos is back with another inside look at the people who keep the internet safe. This time, Amy chats with Ryan Liles, who bridges the gap between Cisco’s product teams and the third-party testing labs that put Cisco products through their paces. Ryan pulls back the curtain on the delicate dance of technical diplomacy, how he keeps his...
How to build an incident response framework
Frameworks provide the structure for an effective incident response program. Here's where to turn for guidance on what to include. - Read more
CVE-2026-20841 Windows Notepad App Remote Code Execution Vulnerability
Added an FAQ and updated the CVSS score. This is an informational change only. - Read more
Cybercrime Ethos: The Shifting Sands of Medical Neutrality
By: Josh Bartolomie, Chief Security Officer, CofenseIntroduction: A Paradigm Shift in Threat Actor BehaviorI have always told myself that I never want to become a stereotypical "stuck in time" security graybeard, the infosec equivalent of "back in my day, we walked to school uphill, both ways, in the snow!" My fear is not of being nostalgic, but that I...
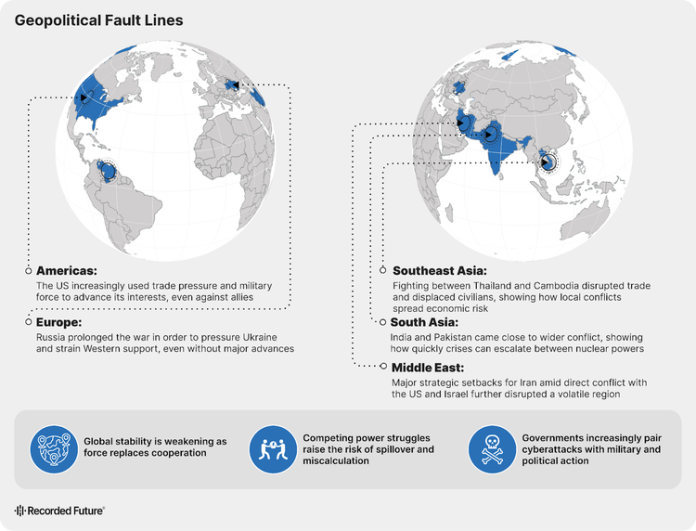
Fragmentation Defined 2025’s Threat Landscape. Here’s What It Means for 2026
Uncertainty has become the operating environment for business. And this year, fragmentation is driving it. The global threat landscape didn't simplify in 2025; it shattered. Geopolitical alliances strained. Criminal enterprises splintered under law enforcement pressure, then regrouped into smaller, faster, and harder-to-track operations. State-sponsored cyber actors shifted from dramatic disruptions to quiet pre-positioning, embedding themselves in networks and...
State of Security Report | Recorded Future
Fragmentation is the new normal The global threat landscape didn't simplify in 2025—it shattered. Geopolitical alliances strained. Criminal enterprises splintered and regrouped. State-sponsored actors shifted from dramatic disruptions to quiet pre-positioning. And as long-established norms unwound, convergence across once-distinct domains created unprecedented uncertainty. The 2026 State of Security report delivers Insikt Group's most comprehensive annual...
VoidLink Framework Enables On-Demand Tool Generation with Windows Plugin Support
A newly tracked intrusion framework called VoidLink is drawing attention for its modular design and focus on Linux systems. It behaves like an implant management framework, letting operators deploy a core implant and add capabilities as needed, which shortens the time from access to action. Recent activity has been linked to a threat actor Cisco refers to as UAT-9921,...
North Korean Hackers Use Deepfake Video Calls to Target Crypto Firms
Campaign combines stolen Telegram accounts, fake Zoom calls and ClickFix attacks to deploy infostealer malware - Read more