Critical BeyondTrust RS vulnerability exploited in active attacks
Researchers warn that a critical vulnerability patched this week in BeyondTrust Remote Support is being exploited in the wild to compromise self-hosted deployments, including Bomgar remote support appliances, which included affected versions of the impacted software. Bomgar, a provider of privileged identity and access management products, acquired BeyondTrust in 2018, adopting the latter’s brand name....
Google Cloud Platform (GCP) Cloud Logging Cross-Tenant Denial of Wallet with Log Analytics
Google Cloud Platform (GCP) Cloud Logging Cross-Tenant Denial of Wallet with Log Analytics Tenable Research has identified and responsibly disclosed a Denial of Wallet (DoW) vulnerability in Google Cloud Logging's Log Analytics. This vulnerability allowed an attacker to force a victim's project to execute massive, expensive BigQuery queries by visiting a maliciously crafted Cloud Logging URL. When a user navigates...
Google Cloud Platform (GCP) Cloud Logging Cross-Tenant BigQuery Leak with Log Analytics
Google Cloud Platform (GCP) Cloud Logging Cross-Tenant BigQuery Leak with Log Analytics Tenable Research has identified and responsibly disclosed a data exfiltration vulnerability in Google Cloud Logging. This flaw allowed an attacker to exfiltrate data from a victim's BigQuery datasets by visiting a maliciously crafted Cloud Logging URL. When a user navigates to a Log Analytics URL, the embedded SQL...
Metasploit Wrap-Up 02/13/2026
SolarWinds Web Help DeskOur very own sfewer-r7 has developed an exploit module for the SolarWinds Web Help Desk vulnerabilities CVE-2025-40536 and CVE-2025-40551. On successful exploitation the session will be as running as NT AUTHORITYSYSTEM. For more information see the Rapid7’s SolarWinds Web Help Desk Vulnerabilities guidance.ContributionsA big thanks to our contributors who have been adding some great content this release. rudraditya21 has added MITRE ATT&CK...
South Korea fines Louis Vuitton, Christian Dior, Tiffany $25M for SaaS security failures
South Korea’s data protection authority has handed down a combined KRW 36 billion (approximately US$25 million) in administrative fines to the local subsidiaries of three global luxury houses, after finding they failed to implement basic security controls while managing customer data through a SaaS platform. The Personal Information Protection Commission (PIPC), South Korea’s top privacy...
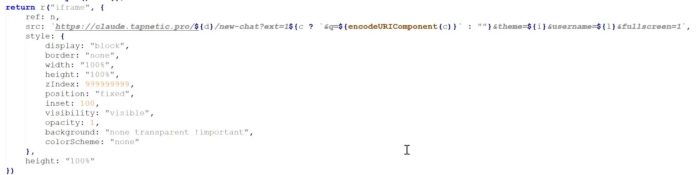
Malicious Chrome AI Extensions Attacking 260,000 Users via Injected IFrames
A coordinated campaign is using malicious Chrome extensions that impersonate popular AI tools like ChatGPT, Claude, Gemini, and Grok. These fake “AI assistants” spy on users through injected, remote-controlled iframes, turning helpful browser add-ons into surveillance tools. More than 260,000 users have installed these extensions. Security researchers identified at least 30 Chrome extensions promoted as AI tools for summarizing,...
Ransomware Groups Claimed 2,000 Attacks in Just Three Months
Ransomware attacks surged 52% in 2025, with supply chain breaches nearly doubling as groups like Qilin drive record monthly incidents worldwide.
The post Ransomware Groups Claimed 2,000 Attacks in Just Three Months appeared first on TechRepublic. - Read more
CVE-2026-21517 Windows App for Mac Installer Elevation of Privilege Vulnerability
Download links fixed - Read more
CVE-2025-59213 Configuration Manager Elevation of Privilege Vulnerability
Updated information to include CVSS scores. This is an informational change only. - Read more
Munich Security Conference: Cyber Threats Lead G7 Risk Index, Disinformation Ranks Third
G7 countries ranked cyber-attacks as the top risk, while BICS members placed cyber threats only as the eighth most pressing risk - Read more