AI in the Middle: Turning Web-Based AI Services into C2 Proxies & The Future Of AI Driven Attacks
Key Points
Check Point Research (CPR) has discovered that certain AI assistants that support web browsing or URL fetching can be abused as covert command-and-control relays (“AI as a proxy”), allowing attacker traffic to blend seamlessly into legitimate, commonly permitted enterprise communications. This technique was demonstrated against platforms such as Grok and Microsoft Copilot, leveraging anonymous web access combined...
[R2] Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2: SC-202602.1 + SC-202602.2
Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2: SC-202602.1 + SC-202602.2 Arnie Cabral Tue, 02/17/2026 - 08:32
Security Center leverages third-party software to help provide underlying functionality. Several of the third-party components (Apache, PHP, libcurl) were found to contain vulnerabilities, and updated versions have been made available by the providers.Out of caution and...
Siemens Simcenter Femap and Nastran
View CSAF
Summary
Siemens Simcenter Femap and Nastran is affected by multiple file parsing vulnerabilities that could be triggered when the application reads files in NDB and XDB formats. If a user is tricked to open a malicious file with any of the affected products, this could lead the application to crash or potentially lead to arbitrary code execution. Siemens has...
Western cyber alliances risk fragmenting in new world order
The conduct of powerful nations is causing knock-on effects in the cyber world as long-standing security frameworks appear increasingly precarious - Read more
Divide and conquer: how the new Keenadu backdoor exposed links between major Android botnets
In April 2025, we reported on a then-new iteration of the Triada backdoor that had compromised the firmware of counterfeit Android devices sold across major marketplaces. The malware was deployed to the system partitions and hooked into Zygote – the parent process for all Android apps – to infect any app on the device. This allowed the Trojan to...
Invitation to Trouble: The Rise of Calendar Phishing Attacks
By: Adrian Andaya and Gabriel Mamaril, Cofense Phishing Defense CenterBefore you click “Accept” on calendar invites, think twice — it could be a phishing scheme. The Cofense Phishing Defense Center (PDC) has identified a new tactic involving fake Microsoft and Google Calendar invites designed to steal your login credentials. Phishing invitations are becoming increasingly sophisticated, often mimicking designs from...
Canada Goose – 581,877 breached accounts
In February 2026, a data breach allegedly containing data relating to Canada Goose customers was published publicly. The data contained 920k records with 582k unique email addresses and included names, phone numbers, IP addresses, physical addresses and partial credit card data, specifically card type and last 4 digits. Canada Goose advised that the data "appears to relate to past...
Unlocking business resilience with full-stack observability in hybrid IT environments
Full-stack observability helps Gulf IT leaders accelerate ROI, strengthen resilience, and advance digital maturity. Learn how to use AI-driven insights and automation to align with business outcomes and sustain competitive advantage. - Read more
University of Pennsylvania – 623,750 breached accounts
In October 2025, the University of Pennsylvania was the victim of a data breach followed by a ransom demand, largely affecting its donor database. After the incident, the attackers sent inflammatory emails to some victims. The data was later published online in February 2026 and included 624k unique email addresses alongside names and physical addresses. For some donor records,...
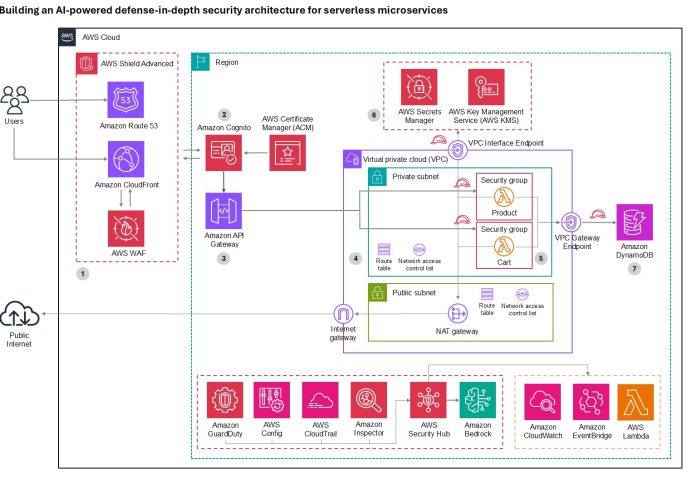
Building an AI-powered defense-in-depth security architecture for serverless microservices
Enterprise customers face an unprecedented security landscape where sophisticated cyber threats use artificial intelligence to identify vulnerabilities, automate attacks, and evade detection at machine speed. Traditional perimeter-based security models are insufficient when adversaries can analyze millions of attack vectors in seconds and exploit zero-day vulnerabilities before patches are available. The distributed nature of serverless architectures compounds this...