[R1] Security Center Version 6.8.0 Fixes Multiple Vulnerabilities
Security Center Version 6.8.0 Fixes Multiple Vulnerabilities Arnie Cabral Wed, 02/18/2026 - 08:32
Security Center leverages third-party software to help provide underlying functionality. Several of the third-party components (php jwt, libssh, postgresql) were found to contain vulnerabilities, and updated versions have been made available by the providers.Out of caution and in line with best practice, Tenable has opted...
“Good enough” emulation: Fuzzing a single thread to uncover vulnerabilities
A Cisco Talos researcher worked around the limitations of hardware-level Code Read-out Protection (RDP) on the Socomec DIRIS M-70 gateway by pivoting from physical debugging to a "good enough" emulation approach. By focusing on emulating only the single thread responsible for Modbus protocol handling rather than the entire system, the author demonstrates how a streamlined emulation strategy can effectively surface vulnerabilities in complex industrial Internet...
Figure – 967,178 breached accounts
In February 2026, data obtained from the fintech lending platform Figure was publicly posted online. The exposed data, dating back to January 2026, contained over 900k unique email addresses along with names, phone numbers, physical addresses and dates of birth. Figure confirmed the incident and attributed it to a social engineering attack in which an employee was tricked into...
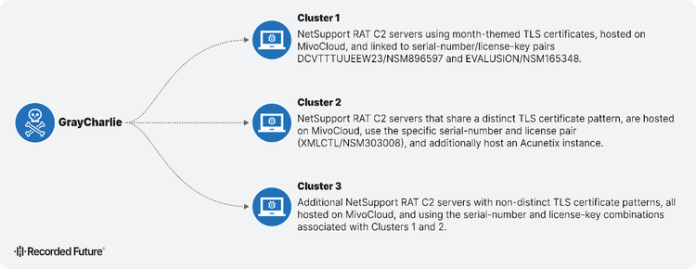
GrayCharlie Hijacks Law Firm Sites in Suspected Supply-Chain Attack
Executive Summary Insikt Group has been monitoring GrayCharlie, a threat actor overlapping with SmartApeSG and active since mid-2023, for some time, and is now publishing its first report on the group. GrayCharlie compromises WordPress sites and injects them with links to externally hosted JavaScript that redirects visitors to NetSupport RAT payloads delivered via fake browser update pages or...
DNS-PERSIST-01: A New Model for DNS-based Challenge Validation
When you request a certificate from Let’s Encrypt, our servers validate that you control the hostnames in that certificate using ACME challenges. For subscribers who need wildcard certificates or who prefer not to expose infrastructure to the public Internet, the DNS-01 challenge type has long been the only choice. DNS-01 works well. It is widely supported and battle-tested, but...
Cyber attacks enabled by basic failings, Palo Alto analysis finds
Cyberattacks are moving faster, shrinking the gap between initial compromise and bad consequences, and the advent of AI is accelerating their timelines in a way that human defenders can no longer keep up with. That’s the broad and perhaps unsurprising finding of Palo Alto Networks’ 2026 Global Incident Response Report, which analyzed 750 incidents in...
Malware in the Wild as Malicious Fork of Legitimate Triton App Surfaces on GitHub
A malicious fork of the legitimate macOS application Triton has surfaced on GitHub, exploiting open-source repositories to distribute malware. The fraudulent repository, created under the account “JaoAureliano,” appeared as a copy of the original Triton app developed by Otávio C. Instead of providing genuine software, the fork redirected users to download a ZIP file containing Windows-based malware. The...
A New Denial-of-Service Vector in React Server Components
React Server Components (RSC) have introduced a hybrid execution model that expands application capabilities while increasing the potential attack surface.
Following earlier disclosures and fixes related to React DoS vulnerabilities, an additional analysis of RSC internals was conducted to assess whether similar denial-of-service risks remained.
This analysis identified a new denial-of-service (DoS) condition that, under specific circumstances, can render a React...