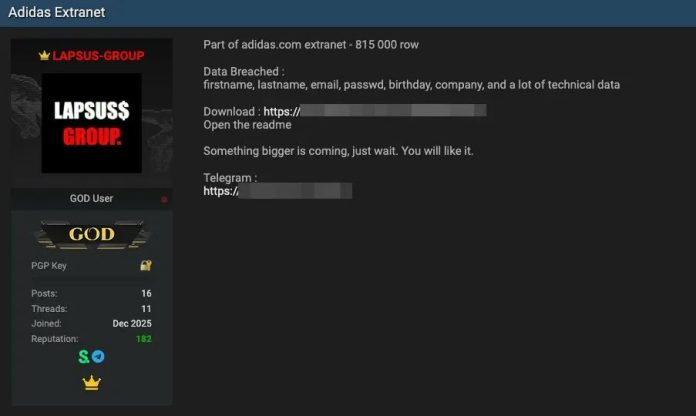
Adidas Investigates Alleged Data Breach – 815,000 Records of Customer Data Stolen
Adidas has confirmed it is actively investigating a potential data breach involving one of its independent third-party partners after a threat actor operating under the alias “LAPSUS-GROUP” posted claims on BreachForums on February 16, 2026, alleging unauthorized access to the sportswear giant’s extranet portal. The actor, believed to be associated with the Scattered Lapsus$ Hunters collective, a group known...
Remcos RAT Expands Real-Time Surveillance Capabilities
New Remcos RAT variant enhances real-time surveillance and evasion techniques to compromise Windows - Read more
CVE-2026-21528 Azure IoT Explorer Information Disclosure Vulnerability
Corrected the CVE description and title. This is an informational change only. - Read more
Figure Data Breach Exposes Nearly 1 Million Customers Online
Fintech lender Figure suffered a social-engineering breach that led to a data dump online. Have I Been Pwned found 967,200 exposed email records.
The post Figure Data Breach Exposes Nearly 1 Million Customers Online appeared first on TechRepublic. - Read more
ICO wins appeal over data protection obligations in Currys cyber attack
The ICO has won an important appeal relating to data protection obligations arising from a 2017-18 cyber attack at electronics retailer Currys PC World. - Read more
EnOcean SmartServer IoT
View CSAF
Summary
Successful exploitation of these vulnerabilities could allow an attacker to remotely execute arbitrary code and bypass ASLR.
The following versions of EnOcean SmartServer IoT are affected:
SmartServer IoT <=4.60.009 (CVE-2026-20761, CVE-2026-22885)
CVSS
Vendor
Equipment
Vulnerabilities
v3 8.1
EnOcean Edge Inc
EnOcean SmartServer IoT
Improper Neutralization of Special Elements used in a Command ('Command Injection'), Out-of-bounds Read
Background
Critical Infrastructure Sectors: Information Technology
Countries/Areas Deployed: Worldwide
Company Headquarters Location: United States
Vulnerabilities
Expand All +
CVE-2026-20761
A...
Jinan USR IOT Technology Limited (PUSR) USR-W610
View CSAF
Summary
Successful exploitation of these vulnerabilities could result in authentication being disabled, a denial-of-service condition, or an attacker stealing valid user credentials, including administrator credentials.
The following versions of Jinan USR IOT Technology Limited (PUSR) USR-W610 are affected:
USR-W610 <=3.1.1.0 (CVE-2026-25715, CVE-2026-24455, CVE-2026-26049, CVE-2026-26048)
CVSS
Vendor
Equipment
Vulnerabilities
v3 9.8
Jinan USR IOT Technology Limited (PUSR)
Jinan USR IOT Technology Limited (PUSR) USR-W610
Weak Password Requirements, Cleartext Transmission of...
Valmet DNA Engineering Web Tools
View CSAF
Summary
Successful exploitation of this vulnerability could allow an unauthenticated attacker to manipulate the web maintenance services URL to achieve arbitrary file read access.
The following versions of Valmet DNA Engineering Web Tools are affected:
Valmet DNA Engineering Web Tools <=C2022 (CVE-2025-15577)
CVSS
Vendor
Equipment
Vulnerabilities
v3 8.6
Valmet
Valmet DNA Engineering Web Tools
Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal')
Background
Critical Infrastructure Sectors: Critical Manufacturing,...
Arkanix Stealer: a C++ & Python infostealer
Introduction
In October 2025, we discovered a series of forum posts advertising a previously unknown stealer, dubbed “Arkanix Stealer” by its authors. It operated under a MaaS (malware-as-a-service) model, providing users not only with the implant but also with access to a control panel featuring configurable payloads and statistics. The set of implants included a publicly available browser post-exploitation tool...
Brand Trust as a Weapon: Multi-Brand Impersonation Campaigns Deliver JWrapper Malware
By: Sean Moleta and Mark Gammad, Cofense Phishing Defense Center In recent threat campaigns, attackers have begun abusing the trust placed in DocuSign, a widely used electronic signature platform, to deliver JWrapper-ackaged malware. By impersonating DocuSign and SimpleHelp communications and embedding malicious executables within seemingly legitimate documents or download links, threat actors trick users into executing harmful payloads. During our analysis...