November 2025 CVE Landscape: 10 Critical Vulnerabilities Show 69% Drop from October
November 2025 saw a significant 69% decrease in high-impact vulnerabilities, with Recorded Future's Insikt Group® identifying 10 vulnerabilities requiring immediate attention, down from...
5 Real-Word Third-Party Risk Examples
Key Takeaways Static vendor checks fall short: Traditional, point-in-time third-party risk management practices (e.g. annual questionnaires) leave organizations blind to emerging vendor...
When the Digital World Turns Physical: The Expanding Role of Threat Intelligence in Executive...
Key Takeaways Cyber and physical risks are converging. Online exposure now translates into real-world danger as doxxing, deepfakes, and...
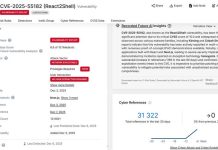
Critical React2Shell Vulnerability Under Active Exploitation by Chinese Threat Actors
Last updated on 9 December. A critical vulnerability in React Server Components is allegedly being actively exploited by multiple Chinese threat actors, Recorded...
The Bug That Won’t Die: 10 Years of the Same Mistake
CVE-2025-55182 Intelligence Card c/o Recorded Future There are now multiple publicly available exploit scripts...
The Hidden Cascade: Why Law Firm Breaches Destroy More than Data
In the wake of the Salesforce/Gainsight breach (kudos to Salesforce for transparently sharing indicators of compromise and updated progress on remediation), third-party cyber...
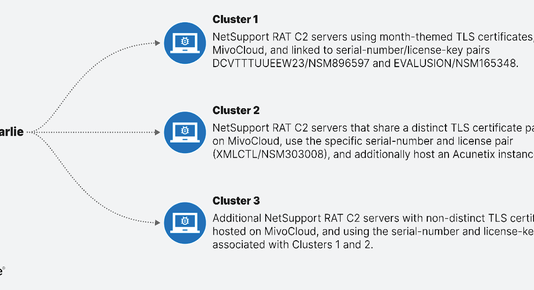
Intellexa’s Global Corporate Web
The author, Julian-Ferdinand Vögele, thanks Amnesty International's Security Lab for its ongoing reporting on the Intellexa and Predator spyware ecosystem. Today,...
The Maturity Gap: The Next Frontier in Threat Intelligence
The Maturity Gap: The Next Frontier in Threat Intelligence ...
Inside the CopyCop Playbook: How to Fight Back in the Age of Synthetic Media
Key Takeaways CopyCop is scaling AI-driven influence operations globally. The Russian influence network known as CopyCop has created more...