Metasploit Wrap-Up 01/16/2025
Persistence, dMSA Abuse & RCE GoodiesThis week, we have received a lot of contributions from the community, such as h00die, Chocapikk and countless others, which is greatly...
Metasploit Wrap-Up 01/16/2026
Persistence, dMSA Abuse & RCE GoodiesThis week, we have received a lot of contributions from the community, such as h00die, Chocapikk and countless others, which is greatly...
Reducing Cloud Chaos: Rapid7 Partners with ARMO to Deliver Cloud Runtime Security
Rapid7 has partnered with ARMO, a leader in cloud infrastructure and application security based on runtime data, to offer Cloud Runtime Security. The new...
Patch Tuesday – January 2026
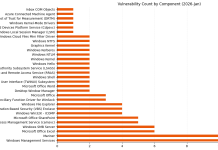
Microsoft is publishing 114 vulnerabilities this January 2026 Patch Tuesday. Today’s menu includes just one vulnerability marked as exploited in the wild, as well...
Metasploit Wrap-Up 01/09/2026
RISC-V PayloadsThis week brings more RISC-V payloads from community member bcoles. One provides a new adapter which allows RISC-V payloads to be converted to commands...
Beyond the Device: Exploring the New Security Risks of Interconnected IoT at CES 2026
Attending CES over the last several years has provided me with a valuable opportunity to observe how rapidly IoT technology continues to evolve across...
Ni8mare and N8scape flaws among multiple critical vulnerabilities affecting n8n
OverviewOn November 18, 2025, a patched release was published for a critical unauthenticated file read vulnerability in n8n, a popular piece of automation software....
Key Takeaways and Top Cybersecurity Predictions for 2026
As the threat landscape keeps shifting, security teams are being asked to do more than react. They are expected to look ahead, connect the...
Metasploit 2025 Annual Wrap-Up
Hard to believe it's that time again, and that Metasploit Framework will see the dawn of another Annual Wrap-Up (and a New Year). All...