Ransomware attacks have gone far beyond simple malicious code. Today, attackers operate with the precision of a well-planned business, using trusted Windows tools to quietly tear down defenses before ransomware even enters the picture.
This shift has made modern ransomware campaigns harder to detect and significantly more damaging.
The tools at the center of this threat were never designed for crime. Utilities such as Process Hacker, IOBit Unlocker, PowerRun, and AuKill were originally built to help IT teams manage processes, unlock files, and troubleshoot everyday system issues.
Attackers have repurposed them to silently terminate antivirus and endpoint detection and response (EDR) software before dropping a ransomware payload.
Since these tools are digitally signed and widely used in enterprise environments, most security systems treat their activity as standard administrative work — leaving very little trace behind.
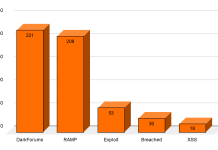
Seqrite researchers identified this growing pattern and noted that the abuse of legitimate low-level tools has become a defining feature of today’s ransomware campaigns — from LockBit 3.0 and BlackCat to Dharma, Phobos, and MedusaLocker.
The research reveals that these threat actors do not rely on custom malware alone. Instead, they carefully study their targets, identify security weaknesses, and weaponize the very tools built to maintain system health.
Disabling antivirus is not a secondary step in these attacks — it is a deliberate and critical part of the overall plan. When security software is active, it can block malicious payloads at execution, capture abnormal encryption behavior, and alert security teams in real time.
By shutting down these defenses first, attackers create a silent window where ransomware can run freely and without interruption.
This strategy has advanced considerably over the years, moving from basic command-line scripts used by early threats like CryptoLocker and WannaCry, to kernel-level driver manipulation seen in Conti and LockBit 2.0 campaigns, and now to prepackaged antivirus killer modules embedded directly into ransomware-as-a-service (RaaS) kits.
The scope of this threat reaches organizations of all sizes — from small businesses to large enterprises — and the attack path consistently follows a deliberate sequence that exploits trusted tools at every stage to avoid detection.
The Two-Stage Abuse of Legitimate Windows Tools
Once attackers establish a foothold, they follow a two-stage process that systematically dismantles security before the ransomware payload ever runs.
In the first stage, the objective is entirely antivirus neutralization and privilege escalation. Tools like IOBit Unlocker delete antivirus binaries using the NtUnlockFile API, while TDSSKiller — originally a rootkit removal utility — is repurposed to unload antivirus kernel drivers, preventing them from reloading.
Process Hacker terminates antivirus processes by exploiting SeDebugPrivilege, and Atool_ExperModel deletes antivirus startup registry entries, removing scheduled tasks and breaking persistence altogether.
The second stage is where the attack reaches its most dangerous point. Once security software has been neutralized, attackers shift focus to credential theft, kernel manipulation, and ransomware deployment.
YDArk hooks kernel-level callbacks to maintain stealth persistence, while PowerRun executes the ransomware payload at full SYSTEM-level privileges.
Mimikatz reads LSASS memory to extract cached administrator credentials, enabling lateral movement across the network.
Unlock_IT erases registry entries and forensic traces to clean up evidence, while AuKill explicitly terminates all remaining EDR processes.
With both stages complete, the environment is fully prepared for silent, large-scale file encryption with no defenses left to intervene.
Organizations should enforce multi-factor authentication on all privileged accounts, enable application whitelisting to block unapproved utilities, and actively monitor for suspicious termination commands such as sc stop, net stop, and taskkill.
Security teams should audit registry changes tied to antivirus and startup configurations, limit access to low-level administrative tools to vetted personnel only, and train SOC analysts to recognize early signs of defense neutralization.
Any affected endpoint should be isolated immediately to prevent lateral movement and contain the impact
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.
The post Hackers Weaponize Legitimate Windows Tools to Disable Antivirus Before Ransomware Attacks appeared first on Cyber Security News.