Analysts at ANY.RUN has identified a sharp spike in phishing campaigns exploiting Microsoft’s OAuth Device Authorization Grant flow, with more than 180 malicious URLs detected within a single week.
Unlike conventional credential harvesting, this technique routes victims through legitimate Microsoft authentication pages, making it substantially harder for security operations centers (SOCs) to catch the compromise in real time.
The OAuth Device Code flow was originally designed for input-constrained devices, such as smart TVs and conference room systems, that cannot easily display a complete browser-based login page. Attackers have repurposed this legitimate mechanism to stage token-based account takeovers that bypass multi-factor authentication entirely.
OAuth Device Code Abuse Attack Chain
The attack chain begins when a threat actor initiates a Microsoft device authorization request, generating two values: a user_code — a short, human-readable string displayed to the victim — and a device_code, an internal session token held exclusively by the attacker.
View sample analysis in ANY.RUN Interactive Sandbox

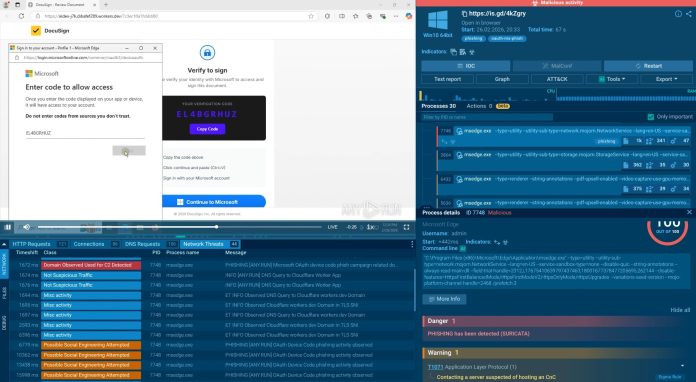
The victim is then directed to a phishing page, typically impersonating a DocuSign document notification, where they are instructed to copy the verification code and enter it at microsoft[.]com/devicelogin.

Because this destination is a genuine Microsoft domain, the victim sees no red flags and often completes MFA normally. By entering the code, the victim unknowingly authorizes a login session that was opened by the attacker, who then receives valid OAuth access and refresh tokens — without ever obtaining a password.
Reduce MTTD and MTTR for phishing attacks. Employ ANY.RUN’s solutions for faster investigations and higher detection rate. Integrate in your SOC
This attack model represents a structural shift that undermines traditional detection logic. The entire compromise occurs over legitimate Microsoft infrastructure, encrypted HTTPS channels, and real authentication pages, none of which trigger standard phishing filters or domain reputation alerts.
For SOC teams, the operational consequences are significant:
- Delayed detection: Compromise may only become visible after suspicious post-access activity surfaces in logs.
- Longer investigations: Analysts must reconstruct token-based access paths rather than trace stolen credentials.
- Higher incident impact: Attackers can access Microsoft 365 email, documents, and shared resources immediately after token issuance.
- Persistent access: Refresh tokens can sustain attacker access long after the initial phishing interaction.
Beyond individual accounts, successful token issuance can enable business email compromise, internal lateral movement, and data exfiltration — all without a single password being stolen.
Sandbox Exposes the Hidden Attack Chain
Phishing pages in this campaign frequently use JavaScript loaders and encrypted HTTPS sessions to hide their real functionality from conventional scanners. ANY.RUN’s Interactive Sandbox addresses this through automatic SSL decryption, which extracts TLS session keys directly from process memory during execution without certificate substitution or traffic disruption. This reveals the actual network requests, hidden scripts, and attacker-controlled API endpoints involved in the phishing flow.
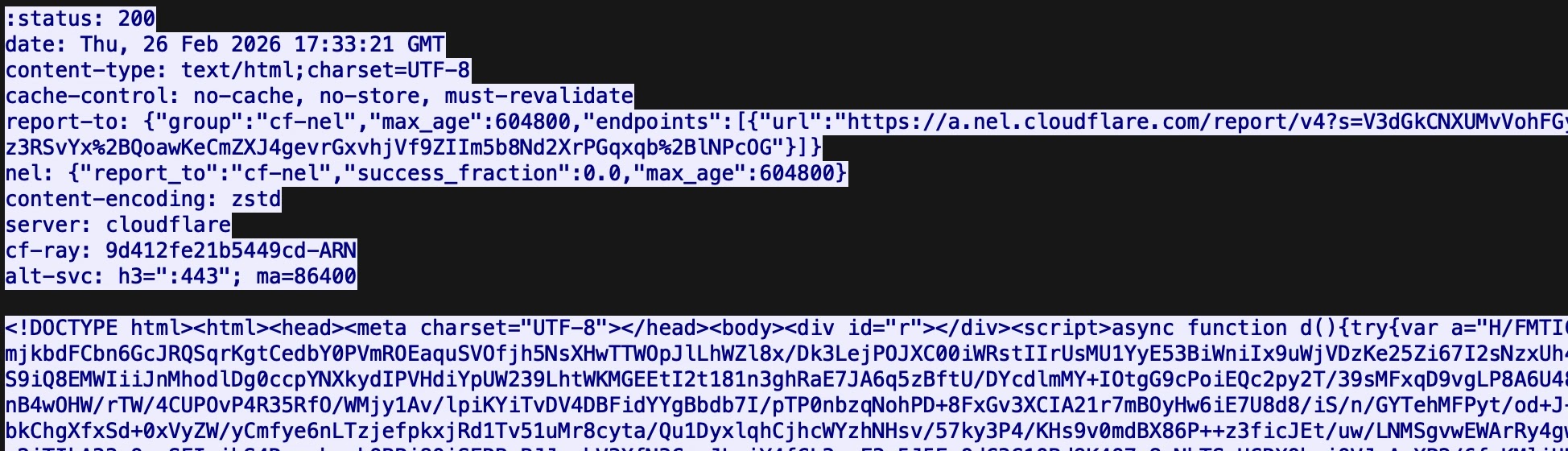
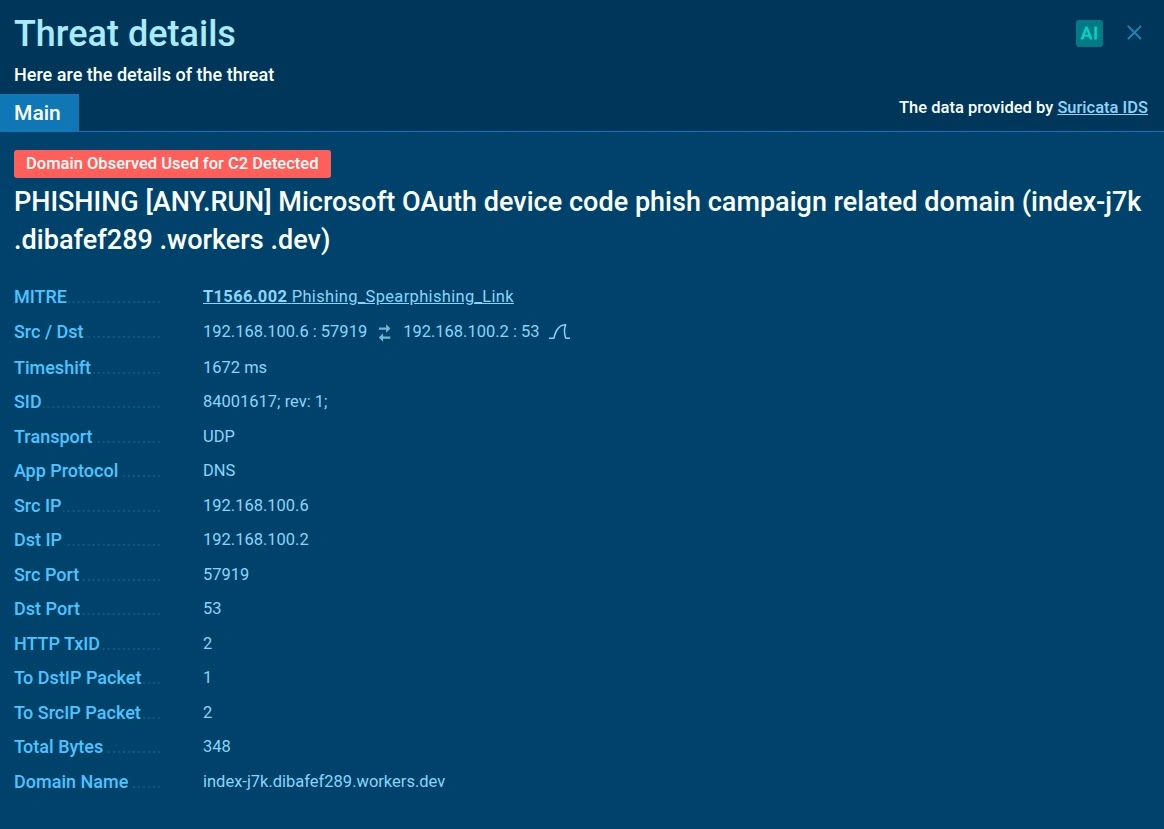
In live analyses of this campaign, SSL decryption exposed specific API calls, including /api/device/start and /api/device/status/, along with a distinctive X-Antibot-Token header used in backend communications.
When these artifacts appear in HTTP requests to non-legitimate hosts, they become high-confidence network indicators that analysts can use to pivot across related infrastructure and map the full campaign footprint.
Suricata IDS rules are also able to fire against this decrypted traffic, turning encrypted phishing sessions into actionable detection signals inside existing SOC tooling.
Defending against OAuth Device Code phishing requires moving beyond domain blocklisting and email filtering. ANY.RUN’s Threat Intelligence Feeds deliver continuously refreshed indicators sourced from live sandbox detonations by thousands of security teams globally, enabling earlier identification of phishing infrastructure before users interact with it.
For triage, analysts can submit suspicious URLs to ANY.RUN’s Interactive Sandbox and observe the complete attack chain in an isolated environment, reducing mean time to detect (MTTD) and mean time to respond (MTTR).
For campaign correlation and threat hunting, ANY.RUN’s Threat Intelligence Lookup allows analysts to query the threat name oauth-ms-phish and immediately surface related domains, files, and infrastructure tied to active campaigns.
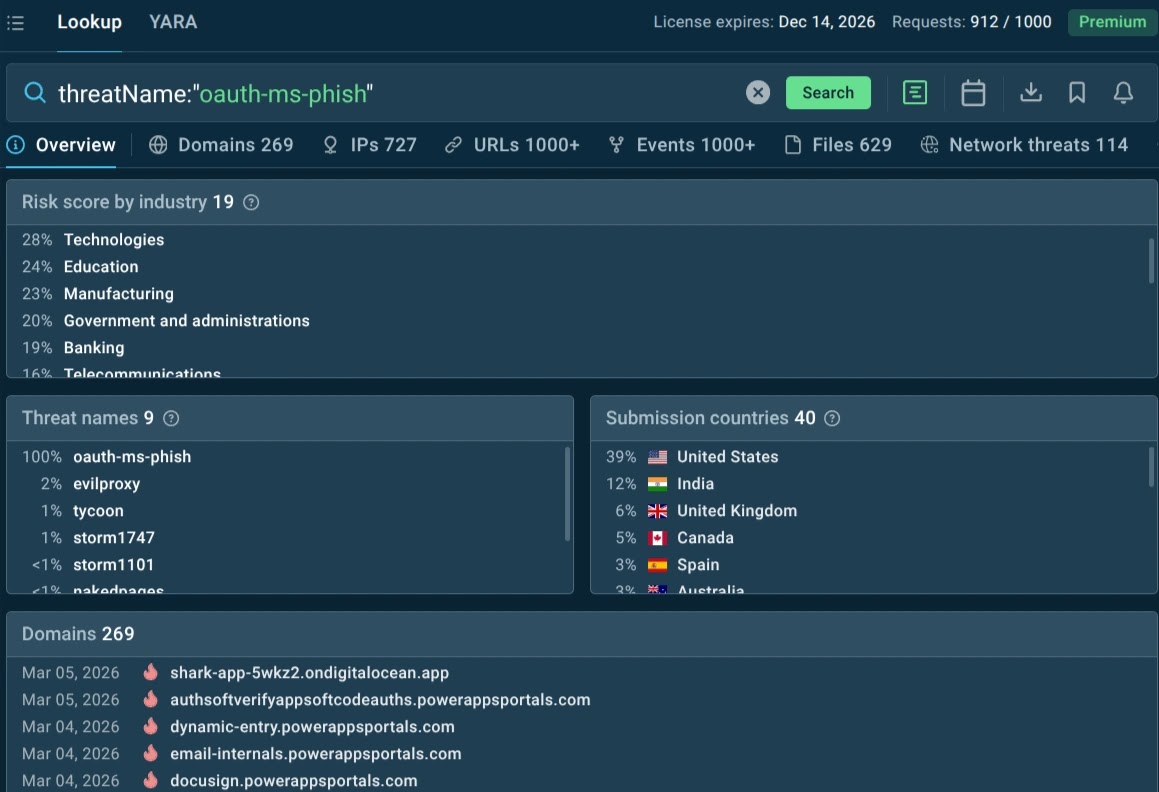
Industries most frequently targeted include Technology, Education, Manufacturing, and Government & Administration, with the United States and India seeing the highest concentration of activity.
Indicators of Compromise (IOCs)
The following Cloudflare Workers domains have been identified as phishing infrastructure in this campaign:[ANY.RUN]
singer-bodners-bau-at-s-account[.]workers[.]devdibafef289[.]workers[.]devab-monvoisinproduction-com-s-account[.]workers[.]devsubzero908[.]workers[.]devsandra-solorzano-duncanfamilyfarms-net-s-account[.]workers[.]devtyler2miler-proton-me-s-account[.]workers[.]devaarathe-ramraj-tipgroup-com-au-s-account[.]workers[.]devrockymountainhi[.]workers[.]devaiinnovationsfly[.]comastrolinktech[.]com
The broader trend confirms what Microsoft itself warned in its 2025 Digital Defense Report: adversaries are increasingly chaining OAuth device code phishing with consent phishing and adversary-in-the-middle techniques, creating layered identity attacks that persist well beyond password resets.
For security leaders, this campaign is a clear signal that identity-layer visibility and encrypted traffic inspection are no longer optional; they are foundational requirements for modern SOC operations.
The post Attackers Hijack Microsoft 365 Accounts Through OAuth Device Code Abuse Without Stealing Passwords appeared first on Cyber Security News.