Microsoft, Europol, and partners have dismantled the Tycoon 2FA phishing-as-a-service (PhaaS) platform, seizing 330 domains used for credential theft and MFA bypass. This coordinated action disrupts a service active since 2023 that powered tens of millions of phishing emails monthly.
Tycoon 2FA enabled cybercriminals to bypass multifactor authentication (MFA) via adversary-in-the-middle (AiTM) techniques, capturing credentials, session tokens, and real-time authentication codes for services like Microsoft 365 and Gmail.
Under a U.S. court order and Europol’s Cyber Intelligence Extension Programme (CIEP), Microsoft led the seizure of control panels and fake login pages, marking the first such cross-border public-private takedown.

The platform accounted for 62% of phishing attempts Microsoft blocked by mid-2025, linking to 96,000 victims, including 55,000 Microsoft customers, with heavy impacts on healthcare and education sectors.
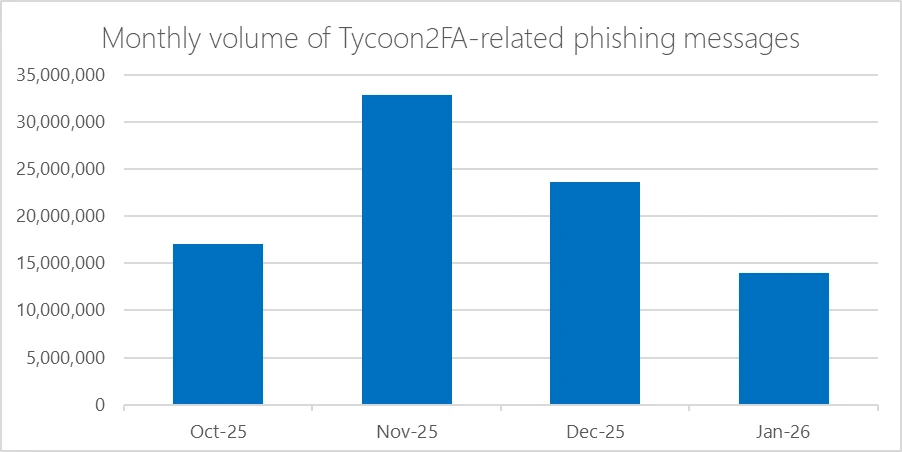
In November 2006, Tycoon 2FA nearly doubled its output from the previous month, likely due to the increase in holiday-season phishing activities and a rise in PhaaS (Phishing as a Service) subscriber activity. This surge resulted in approximately 33 million messages sent in a single month, making it the most prolific phishing service ever tracked by Microsoft.
The significant decline observed in January 2026 indicates a substantial disruption. Between November 2025 and January 2026, the volume of phishing messages fell by roughly 57.6% from its peak. This drop in activity aligns with Microsoft’s infrastructure seizures and coordinated efforts with Europol during that time frame.
Overall, the estimated volume of phishing messages from October 2025 to January 2026 was around 87.5 million, targeting over 500,000 organizations globally.
Over 100 Health-ISAC members were phished, causing operational disruptions like delayed patient care in New York hospitals and schools.
Partners, including Proofpoint, Intel 471, eSentire, Cloudflare, SpyCloud, Resecurity, Coinbase, and Shadowserver, provided telemetry, intelligence, and infrastructure takedowns across jurisdictions like Latvia and the UK.
Tycoon 2FA Phishing Kit Dismantled
Tycoon 2FA used realistic templates, reverse proxies, and dynamic JavaScript to relay victim inputs to legitimate services, hijacking sessions without alerts.
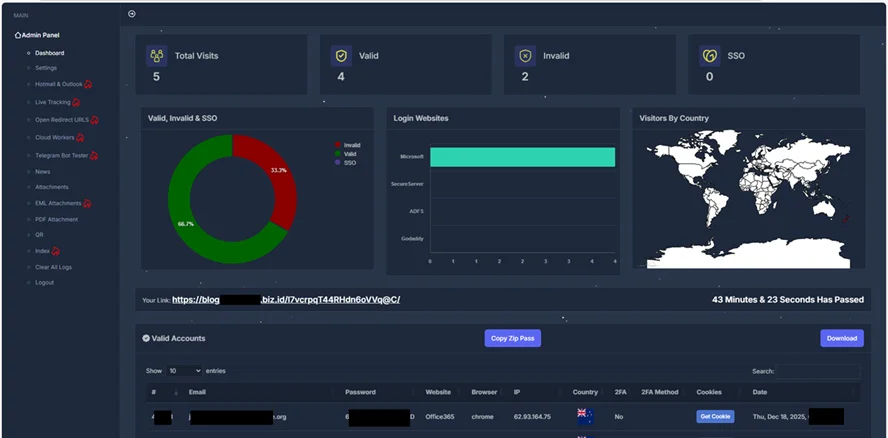
Evasion features included CAPTCHA, bot filtering, browser fingerprinting, Base64/LZ compression, DOM vanishing, and multi-domain redundancy for data exfiltration, according to the Microsoft report.
| IOC Example | Type | Description |
|---|---|---|
| mapbox.stashiowio.us | Credential ingestion | Primary backend for harvested data. |
| date.woosea.biz.id | Exfiltration relay | Secondary data routing domain. |
| ifelse.rlcozx.es | Cross-origin traffic | Obfuscated POST requests. |
Domains favored .ru, .com, and .es TLDs, with rapid rotation and DGA-like generation to evade blocks.
Operated by Saad Fridi (Pakistan-based) with marketing and support partners, it integrated with services like RedVDS for hosting and email spam. This reflects the impersonation economy, where disruptions cascade: prior takedowns of Lumma Stealer, RaccoonO365, and Fake ONNX forced shifts to Tycoon.
MITRE ATT&CK mappings highlight its focus:
| Tactic | Technique | Name |
|---|---|---|
| Reconnaissance | T1598 | Phishing for Information |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
Deploy passkeys, FIDO2 hardware keys, or phishing-resistant MFA over SMS/TOTP; enforce device trust and session controls. Monitor for proxy anomalies, unusual logins, and rapid domain rotations using threat intel feeds.
Block known IOCs and enable AI-driven email filters. Organizations should join ISACs for shared telemetry, as no single entity can counter scalable AiTM PhaaS alone.
Sustained disruptions raise costs for operators, prompting tighter access and shutdowns, reshaping the cybercrime market.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Tycoon 2FA Phishing Kit Disrupted by Microsoft, Europol and Partners appeared first on Cyber Security News.









