Trending Now
Featured news
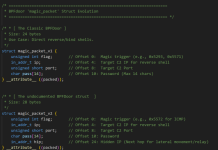
What’s Hiding On Your ICS Network?
What's Hiding On Your ICS Network? #outlook a{ padding:0; } body{ width:100%...
Tech News
Tech
Best Ransomware Detection Tools
Key Takeaways Effective ransomware detection requires three complementary layers: endpoint and extended detection and response (EDR/XDR) to monitor device-level activity, network detection...
Security
My Lovely AI – 106,271 breached accounts
In April 2026, the NSFW AI girlfriend platform My Lovely AI suffered a data breach that exposed over 100k users. The data included user-created...
Most popular
Chromium: CVE-2026-0628 Insufficient policy enforcement in WebView tag
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2024 ) for more information. -...
DDoS’s Newest Minions: IoT Devices (Volume 1)
The latest evolution of cyber weapons is brought to you by the default passwords in Internet of Things (IoT) devices. - Read more