Trending Now
Featured news
Security by Design: Why Multi-Factor Authentication Matters More Than Ever
In an era marked by escalating cyber threats and evolving risk landscapes, organisations face mounting pressure to strengthen their security posture whilst maintaining seamless...
Tech News
Tech
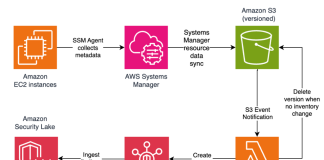
File integrity monitoring with AWS Systems Manager and Amazon Security Lake
Customers need solutions to track inventory data such as files and software across Amazon Elastic Compute Cloud (Amazon EC2) instances, detect unauthorized...
Security
Rockwell Automation ArmorStart LT
View CSAF
Summary
Successful exploitation of these vulnerabilities could allow an attacker to cause a denial-of-service condition.
The following versions of Rockwell Automation ArmorStart LT are affected:
ArmorStart...
Most popular
Versa Concerto SD-WAN Authentication Bypass
What is the Vulnerability? A critical security vulnerability (CVE-2025-34026) has...
Centrify Named a Visionary in the 2018 Magic Quadrant for Access Management, Worldwide
Download the 2018 Gartner Magic Quadrant for Access Management
Centrify has been named a Visionary by Gartner, Inc. in the 2018 Magic Quadrant for Access...
MUT-4831: Trojanized npm packages deliver Vidar infostealer malware
Analysis of a threat actor campaign targeting Windows users with Vidar infostealer malware via malicious npm packages - Read more
How Cisco Talos powers the solutions protecting your organization
Cisco Talos is Cisco’s threat intelligence and security research organization that powers Cisco’s product portfolio with that intelligence. While we are well known for the security research...