Summary
- Quantum computing is moving from theory toward early practical use, with direct implications for encryption, authentication, and long-term data confidentiality.
- The primary risk is the eventual emergence of cryptographically relevant quantum computers (CRQCs), which would break today’s public-key cryptography and undermine encryption, digital identity, and software trust at scale.
- Quantum risk is already present: “harvest now, decrypt later” activity exposes long-lived sensitive data today, regardless of when CRQCs ultimately arrive.
- Regulatory mandates and procurement standards are accelerating post-quantum cryptography (PQC) adoption, making quantum readiness a multi-year compliance and resilience priority.
- Organizations that delay preparation beyond 2026 are likely to face compressed migration timelines, higher transition costs, and increased operational disruption.
Quantum Computing Explained
Quantum computing applies principles of physics to solve certain complex problems far more efficiently than classical computers. Its security relevance lies primarily in cryptanalysis and optimization: A sufficiently powerful quantum computer will reduce the calculations required to protect today’s public-key encryption from thousands of years to hours or less. Researchers have used the term “Q-Day” to refer to the hypothetical point at which quantum computers will be powerful enough to break encryption.
Quantum computing is now moving from theory toward early practical use, bringing “Q-Day” closer to reality. Industry estimates suggest quantum computing alone could generate up to $1.3 trillion in value by 2035. Major cloud providers, including IBM, Google, and Microsoft, are expanding their quantum services, while specialised firms such as Quantinuum and PsiQuantum continue to improve system stability and error correction. While these advances are not yet transformative, they are consistent with the early stages of commercial adoption.

Alongside its potential benefits across finance, pharmaceuticals, defense, and other sectors, quantum computing introduces four key security risks.
Risk 1: Breaking Public-Key Encryption
The most critical risk is the eventual arrival of cryptographically relevant quantum computers (CRQCs), systems capable of breaking widely used public-key algorithms such as RSA, Elliptic Curve Cryptography (ECC), and Diffie-Hellman. These algorithms underpin internet communications (Transport Layer Security [TLS], virtual private networks [VPNs], Secure Shell [SSH]), identity and access management, industrial and internet-of-things (IoT) systems, and the integrity of software supply chains.
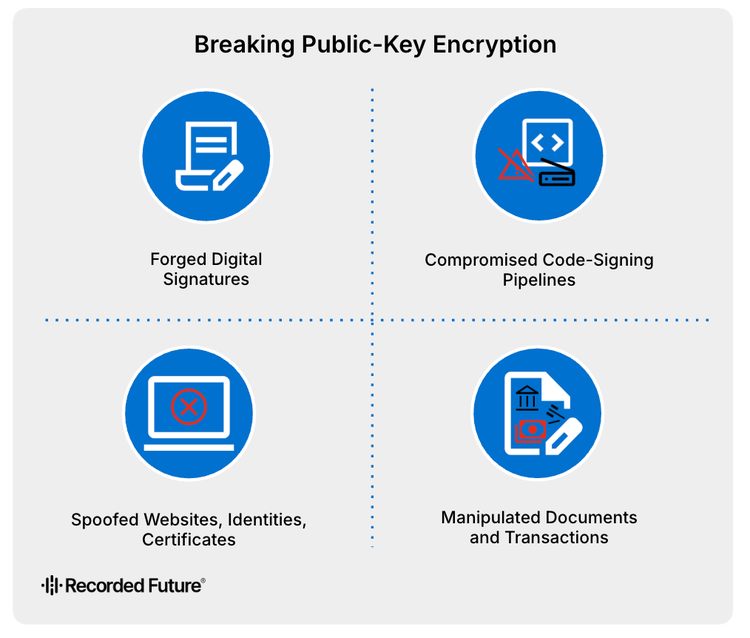
If broken, threat actors could decrypt sensitive data, impersonate trusted systems, and undermine digital authentication. This could enable:
- Forged digital signatures
- Compromised code-signing pipelines
- Spoofed websites, identities, and certificates
- Manipulated financial transactions and legal documents
Risk 2: Harvest Now, Decrypt Later (HNDL)
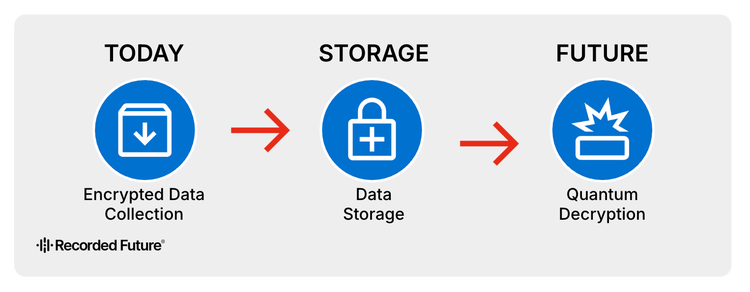
Although cryptographically relevant quantum computers (CRQCs) may still be years away, the risk is already materializing through “harvest now, decrypt later” (HNDL) activity. State-sponsored threat actors are likely collecting and storing encrypted data today with the intent to decrypt it once quantum capabilities mature. A 2021 Booz Allen Hamilton assessment found that Chinese economic espionage operations are likely targeting encrypted data with long-term intelligence value, including biometric identifiers, covert source identities, and weapons designs.
Large-scale routing manipulation offers one method for intercepting such data. Researchers at the US Naval War College and Tel Aviv University documented systematic Border Gateway Protocol (BGP) hijacking by China Telecom between 2016 and 2019, which redirected traffic from US, Canadian, and Scandinavian networks through Chinese infrastructure. These types of operations align with a long-term HNDL collection strategy.
Under the HNDL model, exposure occurs at the moment data is transmitted or stored, not when it is eventually decrypted. The primary risk, therefore, centers on long-lived data: information that must remain confidential for a decade or more, or whose sensitivity does not diminish over time, such as government and national security records, intellectual property and trade secrets, personal identifiers, financial data, biometric templates, healthcare records, and legal archives. For these data classes, compromise may not be immediately visible, but once decrypted, the consequences are irreversible. As a result, organizations holding long-lived sensitive data face near-term strategic risk regardless of when CRQCs become operational.
Large-scale routing manipulation offers one method for intercepting such data. Researchers at the US Naval War College and Tel Aviv University documented systematic Border Gateway Protocol (BGP) hijacking by China Telecom between 2016 and 2019, which redirected traffic from US, Canadian, and Scandinavian networks through Chinese infrastructure. These types of operations align with a long-term HNDL collection strategy.
Under the HNDL model, exposure occurs at the moment data is transmitted or stored, not when it is eventually decrypted. The primary risk, therefore, centers on long-lived data: information that must remain confidential for a decade or more, or whose sensitivity does not diminish over time, such as government and national security records, intellectual property and trade secrets, personal identifiers, financial data, biometric templates, healthcare records, and legal archives. For these data classes, compromise may not be immediately visible, but once decrypted, the consequences are irreversible. As a result, organizations holding long-lived sensitive data face near-term strategic risk regardless of when CRQCs become operational.
Risk 3: Quantum-Accelerated Brute-Force Attacks (Grover’s Algorithm)
Quantum computing does not break modern symmetric encryption outright, but it can accelerate search-intensive tasks through techniques such as Grover’s algorithm. This reduces defender reaction time and increases the effectiveness of weak or legacy cryptographic implementations. In practice, this could enable faster brute-force attempts against outdated encryption, quicker identification of exposed secrets or misconfigurations, and more efficient malware tuning and exploit development.
Recent demonstrations, such as Silicon Quantum Computing’s high-accuracy implementation on a four-qubit processor, remain limited in scale but reflect steady progress toward these capabilities. However, Grover’s algorithm is constrained by high hardware requirements and limited parallelization. As a result, modern symmetric algorithms such as AES-128/192/256 are expected to remain secure for the foreseeable future, while environments with poor cryptographic hygiene will be affected first.
Risk 4: Quantum- and AI-Enhanced Vulnerability Discovery
Quantum capability will not develop in isolation. As quantum systems improve optimization and search performance, and AI automates reconnaissance, exploit development, and lateral movement, adversaries are likely to operate at unprecedented speed and scale. Rather than identifying isolated weaknesses, attackers could rapidly map entire attack surfaces, chain misconfigurations, and deploy optimized malware variants in near real time. Research from 2024 demonstrates that machine-learning classifiers can already recover full cryptographic keys from PQC implementations using only a few hundred power traces, underscoring that even post-quantum algorithms will require hardened deployment.
This convergence of AI and quantum technologies could significantly increase an attacker’s operational tempo and amplify the impact of individual security lapses. The risk is compounded by the fact that a rising number of organizations carry substantial security debt, with many reporting slow remediation cycles that leave vulnerabilities exposed for extended periods.
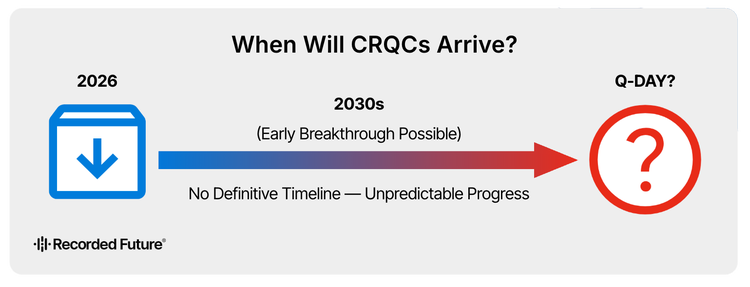
When Will CRQCs Arrive?
There is no definitive timeline for CRQCs. Most projections place their arrival in the mid-to-late 2030s, with credible breakthroughs possible earlier in the decade. These estimates should be treated with caution: forecasting is inherently uncertain because progress in quantum error correction and qubit scaling occurs in uneven advances rather than linear progression.
For security leaders, the precise date of “Q-Day” is less important than the lifecycle of deployed systems. Infrastructure implemented today may remain operational when CRQCs emerge. Current cryptographic decisions are therefore future-binding.
Under the HNDL model, quantum risk is already material for long-lived data. Preparedness, visibility, and cryptographic agility matter more than timeline prediction.
How Should Organizations Prepare?
The transition to post-quantum cryptography (PQC) is no longer a theoretical exercise. It is increasingly driven by regulation, procurement requirements, and emerging industry norms. These developments should be interpreted as operational signals necessitating forward planning.
In the US, the Quantum Computing Cybersecurity Preparedness Act requires federal agencies to inventory quantum-vulnerable cryptography and develop migration plans. NIST’s 2024 PQC standards now set the baseline for federal procurement and are rapidly becoming global reference points. In parallel, Commercial National Security Algorithm (CNSA) 2.0 defines approved algorithms and transition timelines for national security systems, with full migration targeted by 2035. Similar momentum is building in Europe. The EU Cybersecurity Act and national quantum-preparedness strategies are accelerating early adoption, particularly across critical infrastructure sectors such as energy and transportation.
Although many of these mandates formally apply to public-sector systems, their practical impact extends well beyond government. Procurement requirements and supply-chain expectations are translating policy into commercial pressure. As a result, cryptographic inventory, structured migration planning, vendor alignment, and crypto-agility are likely to become baseline governance expectations rather than optional best practices. Boards are beginning to treat quantum risk as a strategic planning issue, not a distant technical concern, with some sectors allocating dedicated quantum-security budgets approaching 5% of total cybersecurity spend to support preparation.
Industry coordination further reinforces this direction of travel. Financial institutions, payment networks, and telecommunications providers are forming quantum-readiness working groups to align migration timelines and manage shared dependencies. SWIFT is developing PQC migration guidance for its global messaging network, and Mastercard has released a PQC migration white paper outlining practical transition steps.
As the HNDL risk window narrows, organizations that begin structured preparation now are likely to manage transition risk deliberately and cost-effectively. Security leaders should ensure they understand where quantum-vulnerable cryptography resides, how regulatory obligations may cascade through customers and partners, and whether critical suppliers have credible PQC transition roadmaps. Those that delay risk compressed timelines, regulatory pressure, and materially higher transition costs later in the decade. Specific technical and governance steps are detailed in the Mitigations section.
Outlook
HNDL activity will continue to expand.
State-sponsored threat actors are highly likely to increase long-term interception and storage of encrypted data, particularly from sectors handling information with long confidentiality lifetimes. Even as storage economics fluctuate, scalable interception infrastructure and economically sustainable long-term storage models enable continued accumulation of high-value encrypted material. Demonstrated routing manipulation capabilities further support persistent collection at scale, ensuring exposure continues to build regardless of when CRQCs ultimately arrive.
Attacker operational tempo will increase.
The convergence of AI-enabled automation with quantum-accelerated search and optimization is likely to compress defender response windows and amplify the impact of existing security debt. Organizations reliant on legacy cryptography and slow remediation cycles will feel this pressure first.
Regulatory and procurement pressure will intensify.
Post-quantum readiness is increasingly likely to become a baseline requirement for regulated markets, government contracts, and high-trust supply chains. US and European initiatives are formalizing transition timelines, and these mandates will propagate through vendor ecosystems, reframing quantum preparedness as a competitive requirement rather than a discretionary control.
Migration risk will become a primary enterprise challenge.
Organizations that delay cryptographic inventories and crypto-agility investments are likely to face compressed transition timelines, higher costs, and greater operational disruption as standards mature and vendor dependencies shift.
Mitigations
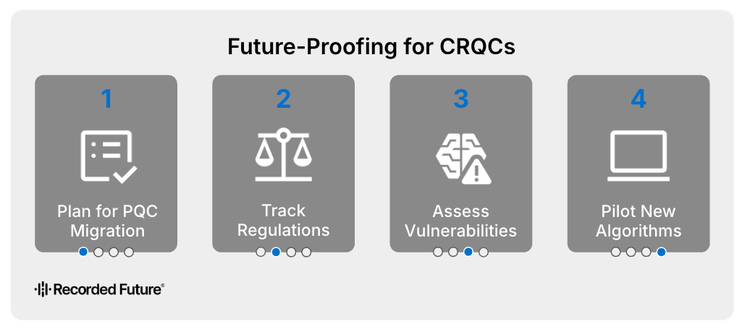
Organizations should treat quantum resilience as a phased program aligned to visibility, flexibility, and systemic risk reduction, with leaders actively testing assumptions at each stage.
Short-term (2026): Establish visibility and prioritization
Security teams should maintain a comprehensive cryptographic inventory, identifying quantum-vulnerable algorithms across applications, infrastructure, and third-party dependencies, as well as public key infrastructure (PKI), operational technology, and IoT environments, and mapping them to data sensitivity and confidentiality requirements.
Leaders should be asking:
- Do we have an enterprise-wide inventory of where quantum-vulnerable cryptography is embedded, including in legacy and third-party systems?
- Which data assets must remain confidential for a decade or more, and are they currently protected by algorithms likely to be broken by CRQCs?
Medium-term (2026–2028): Enable flexibility
Organizations should design for cryptographic agility, ensuring that new systems and major upgrades allow algorithm replacement without architectural redesign. Vendors supporting long-lived products should provide credible PQC transition roadmaps aligned to emerging standards.
Leaders should be asking:
- Are we continuing to deploy systems that hard-code cryptographic algorithms, thereby increasing future migration risk?
- Do our critical suppliers have credible, time-bound PQC transition plans, and how exposed would we be if they fell behind?
Long-term (2028-onwards): Reduce systemic exposure
Migration should prioritize long-lived data and high-trust functions, including identity infrastructure, code signing, certificate management, secure build pipelines, and critical third-party software. Strengthening software and supply-chain integrity will be essential to minimizing cascading risk during transition.
CISOs should be asking:
- Which enterprise trust anchors (for example, certificate authorities, signing keys, or hardware security modules) would create systemic impact if rendered vulnerable in a post-quantum scenario?
- Can we rotate and replace cryptographic components at scale without operational disruption if migration timelines compress unexpectedly?
Recorded Future intelligence can support these efforts by tracking emerging cryptographic risks through our Threat Intelligence Module, identifying exposed dependencies through our Attack Surface Intelligence, and assessing third-party quantum readiness as standards and vendor capabilities evolve through our Third-Party Intelligence Module.
Risk Scenario
GridCore Systems is a US-based provider of industrial control systems (ICS) and grid-management software for electric utilities nationwide. The firm relies on quantum-vulnerable public-key cryptography (RSA/ECC) for remote access, software signing, and secure data exchange with utilities and regulators, and has not yet completed a post-quantum cryptographic transition.
First-Order Implications
Threat
Risk
- Legal or compliance failure: Exposure of regulated energy-sector data triggers scrutiny under North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) and federal cybersecurity requirements.
- Operational disruption: Incident response and emergency access restrictions delay maintenance and update cycles for utility customers.
- Brand impairment: Disclosure of quantum-readiness gaps undermines customer and regulator confidence.
Second-Order Implications
Threat
Risk
- Operational disruption: Utilities delay deployments and require additional validation of software integrity and access controls.
- Brand impairment: Public concerns over update authenticity erode GridCore’s reputation as a trusted infrastructure provider.
- Competitive disadvantage: Customers begin to favor vendors with demonstrable post-quantum migration progress.
Third-Order Implications
Threat
Risk
- Operational disruption: Adversaries plan targeted intrusions or disrupt contingencies during periods of geopolitical tension.
- Legal or compliance failure: Retroactive exposure of protected data leads to long-term regulatory action and contractual liability.
- Competitive disadvantage: GridCore loses preferred-vendor status and future contracts to quantum-ready competitors.













