|
What is the Attack? |
A software supply chain attack targeted the widely used JavaScript library Axios after an attacker reportedly compromised a maintainer’s npm account and published malicious package versions 1.14.1 and 0.30.4. These versions introduced a concealed dependency, plain-crypto-js@4.2.1, which executed during installation and deployed a cross-platform remote access trojan (RAT). Axios is a widely adopted HTTP client for both browser and Node.js environments, with more than 100 million weekly downloads and extensive use across: – Web applications The malicious versions were available for approximately 2–3 hours before being removed. Any system that executed npm install during that period and retrieved the affected versions should be treated as potentially fully compromised. This is a high-impact software supply chain compromise that abused a trusted package distribution channel. By using a hidden dependency and install-time execution, the attacker enabled automated compromise at scale, with particular risk to developer workstations, build servers, and software delivery pipelines. |
|
What is the recommended Mitigation? |
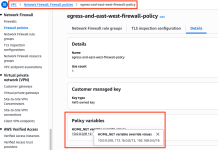
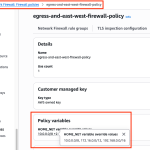
To mitigate this vulnerability, users of affected packages should immediately downgrade to safe versions and audit their environments for indicators of compromise. Treat affected systems as fully compromised and perform the following actions:
|
|
What FortiGuard Coverage is available? |
|
Welcome!Log into your account