February 2026 saw a 43% decrease in high-impact vulnerabilities, with Recorded Future’s Insikt Group® identifying 13 vulnerabilities requiring immediate remediation, down from 23 in January 2026. All 13 carried a Very Critical Recorded Future Risk Score.
What security teams need to know:
- Microsoft dominates: Six of 13 vulnerabilities affected Microsoft products, accounting for 46% of February’s findings; all were added to CISA’s KEV catalog on the same day
- Supply-chain attack on Notepad++: Lotus Blossom, a suspected China state-sponsored threat actor, exploited CVE-2025-15556 to hijack Notepad++’s update channel and deliver a Cobalt Strike Beacon and the Chrysalis backdoor
- APT28 exploits MSHTML flaw: The Russian state-sponsored group leveraged CVE-2026-21513 via malicious Windows Shortcut files for multi-stage payload delivery
- Public exploits available: Four of 13 vulnerabilities have publicly available proof-of-concept code; an alleged exploit for a fifth is being advertised for sale
Bottom line: Despite a 43% drop in volume, February’s vulnerabilities include named threat actor exploitation and five RCE-enabling flaws, making prioritized, intelligence-driven remediation as important as ever.
Quick Reference: February 2026 Vulnerability Table
All 13 vulnerabilities below were actively exploited in February 2026.
Score
Table 1: List of vulnerabilities that were actively exploited in February based on Recorded Future data. *An alleged exploit for CVE-2026-21533 is being advertised for sale across Github. Recorded Future Triage was used to browse the website advertising the exploit, which can be viewed here via the Replay Monitor. (Source: Recorded Future)
Key Trends: February 2026
Vendors Most Affected
- Microsoft led with six vulnerabilities across Windows, Windows Server, Office, and Microsoft 365 products
- BeyondTrust faced a critical OS command injection flaw in Remote Support (RS) versions 25.3.1 and earlier, and Privileged Remote Access (PRA) versions 24.3.4 and earlier
- Cisco saw active exploitation of an authentication bypass in Catalyst SD-WAN infrastructure
- Additional affected vendors: Notepad++, Apple, Soliton Systems K.K., Google, and Dell
Most Common Weakness Types
- CWE-78 – OS Command Injection (tied for most common)
- CWE-693 – Protection Mechanism Failure (tied for most common)
- CWE-476 – NULL Pointer Dereference
- CWE-843 – Type Confusion
- CWE-807 – Reliance on Untrusted Inputs in a Security Decision
Exploitation Activity
Vulnerabilities associated with malware campaigns:
- Lotus Blossom (suspected China state-sponsored) exploited CVE-2025-15556 to hijack Notepad++ update traffic between June and December 2025. The campaign rotated C2 servers across three attack chains to deliver a Metasploit loader, Cobalt Strike Beacon, and a custom backdoor called Chrysalis.
- APT28 (Russian state-sponsored) exploited CVE-2026-21513 using malicious Windows Shortcut (.lnk) files with embedded HTML payloads for multi-stage payload delivery, with observed network communication to infrastructure associated with the threat group.
- UNC6201 (suspected China-nexus) exploited CVE-2026-22769 to compromise Dell RecoverPoint for VMs appliances, deploying the SLAYSTYLE web shell, BRICKSTORM backdoor, and GRIMBOLT, a C#-based backdoor with native AOT compilation to complicate detection.
Long-running exploitation activity:
- UAT-8616 exploited CVE-2026-20127, chaining it with CVE-2022-20775 to achieve root-level access on Cisco Catalyst SD-WAN systems, with Cisco Talos attributing the activity to a sophisticated threat actor and assessing that the activity dates back to at least 2023.
Priority Alert: Active Exploitation
These vulnerabilities demand immediate attention due to confirmed exploitation in the wild.
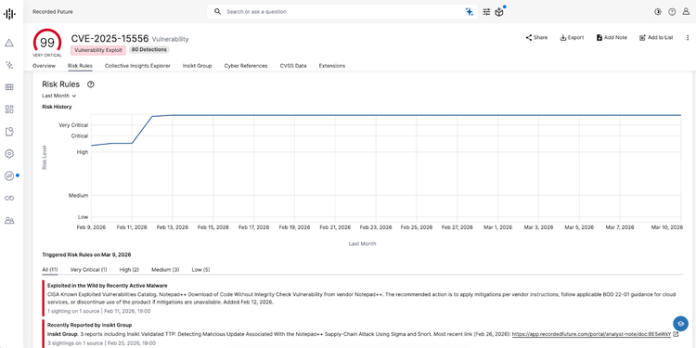
CVE-2025-15556 | Notepad++
Risk Score: 99 (Very Critical) | CISA KEV: Added February 12, 2026
Why this matters: Lotus Blossom exploited this flaw to replace legitimate Notepad++ update packages with malicious installers, deploying Cobalt Strike and the Chrysalis backdoor to targeted users over a six-month period. The vulnerability affects the WinGUp updater used by Notepad++ versions prior to 8.8.9, which fails to cryptographically verify downloaded update metadata and installers.
Affected versions: Notepad++ versions prior to 8.8.9 (version 8.9.1 recommended)
Immediate actions:
- Update to Notepad++ version 8.9.1, released January 26, 2026
- Hunt for the malicious update.exe sample (SHA256: 4d4aec6120290e21778c1b14c94aa6ebff3b0816fb6798495dc2eae165db4566) in your environment
- Monitor for GUP.exe spawning unexpected child processes
- Review network connections for traffic to 45[.]76[.]155[.]202, 45[.]77[.]31[.]210, 45[.]32[.]144[.]255, or 95[.]179[.]213[.]0
- Check for directories named ProShow under %APPDATA% or unexpected files in %APPDATA%\Adobe\Scripts\
- Block or alert on curl.exe uploading files to temp[.]sh
Known C2 infrastructure: 45[.]76[.]155[.]202, 45[.]77[.]31[.]210, cdncheck[.]it[.]com, safe-dns[.]it[.]com, 95[.]179[.]213[.]0
Detection resources: Insikt Group created Sigma rules to detect update.exe’s execution of reconnaissance commands (whoami, tasklist, systeminfo, and netstat -ano) and curl commands for system information exfiltration, available to Recorded Future customers.