Implementing HTTP Strict Transport Security (HSTS) across AWS services
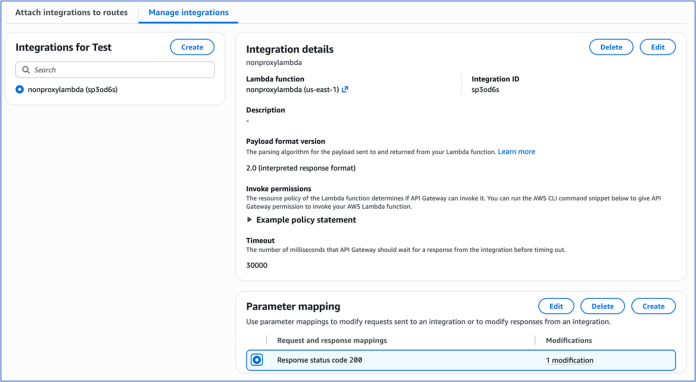
Modern web applications built on Amazon Web Services (AWS) often span multiple services to deliver scalable, performant solutions. However, customers encounter challenges when implementing a cohesive HTTP Strict Transport Security (HSTS) strategy across these distributed architectures. Customers face fragmented security implementation challenges because different AWS services require distinct approaches to HSTS configuration, leading to inconsistent security postures.Applications...
Meet digital sovereignty needs with AWS Dedicated Local Zones expanded services
At Amazon Web Services (AWS), we continue to invest in and deliver digital sovereignty solutions to help customers meet their most sensitive workload requirements. To address the regulatory and digital sovereignty needs of public sector and regulated industry customers, we launched AWS Dedicated Local Zones in 2023, with the Government Technology Agency of Singapore (GovTech Singapore) as...
Adversarial Poetry and the Efficacy of AI Guardrails
We investigate the rise of adversarial poetry in AI security. Understand how metaphor-based exploits circumvent guardrails and the defenses we need for LLMs moving forward. - Read more
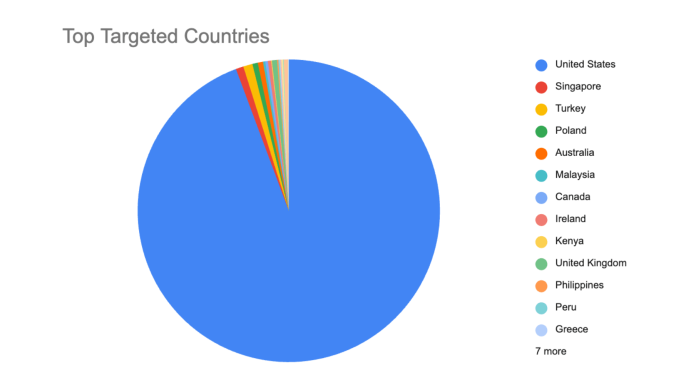
Chain Reaction: Attack Campaign Activity in the Aftermath of React Server Components Vulnerability
Introduction and Vulnerability Overview
Earlier this month, Imperva published an initial advisory outlining how our customers were protected against the newly disclosed React2Shell vulnerability impacting React Server Components (RSC). That post focused on the essentials: a critical flaw arising from unsafe server-side deserialization of client-controlled RSC payloads, its potential to enable unauthenticated remote code execution, and what we do to protect against it.
In this follow-up, we expand on that foundation by...
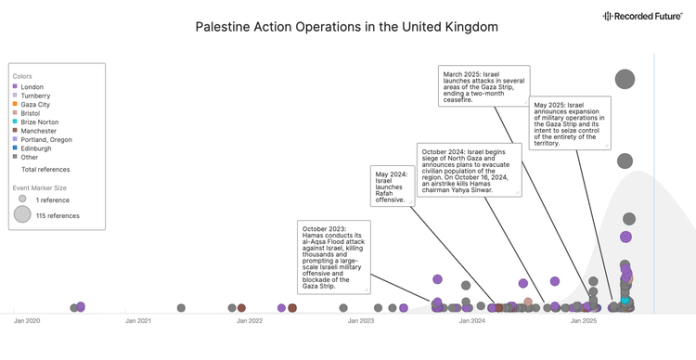
Palestine Action: Operations and Global Network
Executive Summary Palestine Action has almost certainly responded to its July 2025 designation as a terrorist organization in the United Kingdom (UK) by encouraging domestic violent extremists (DVEs) outside the UK with a nexus to the group to increase the scope and frequency of their operations, while abstaining from conducting or claiming attacks within the UK. Palestine Action’s...
The Privacy Gap in API Security: Why Protecting APIs Shouldn’t Put Your Data at Risk
The more critical APIs become, the more sensitive data they carry identities, payment details, health records, customer preferences, tokens, keys, and more.
And this is where organizations face a painful, often invisible problem:
To protect APIs, many organizations end up exposing the very data they are trying to secure.
Most API security tools still rely on raw-payload logging, traffic replay, or shipping...
Implications of Russia-India-China Trilateral Cooperation
Executive Summary Insikt Group assesses that the August 2025 meeting of Chinese Communist Party (CCP) General Secretary Xi Jinping, Indian Prime Minister Narendra Modi, and Russian President Vladimir Putin at the Shanghai Cooperation Organization (SCO) Summit likely suggests early interest among the three states to explore trilateral cooperation, though the formation of a resilient bloc remains unlikely. United...
Investigating an adversary-in-the-middle phishing campaign targeting Microsoft 365 and Okta users
In this post, we investigate a recent phishing campaign that targets Microsoft 365 users. - Read more
OS command injection in multiple endpoints
CVSSv3 Score: 7.0
An Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') vulnerability in FortiSandbox may allow an authenticated attacker to execute unauthorized code on the underlying system via crafted HTTP requests.
Revised on 2025-12-09 00:00:00
- Read more
OS command injection in GUI backup options
CVSSv3 Score: 6.9
An improper neutralization of special elements used in an OS command ('OS Command Injection') vulnerability in FortiSandbox GUI may allow an authenticated privileged attacker to execute unauthorized code or commands via crafted HTTP or HTTPS requests.
Revised on 2025-12-09 00:00:00
- Read more