Cyber Security Report 2026
Check Point Research continuously investigates real-world attacks, vulnerabilities, attackers’ infrastructure, and emerging techniques across global networks and environments. The Cyber Security Report 2026 consolidates our research efforts throughout 2025 to deliver a clear, data-driven view of the current threat landscape and its trajectory in 2026. As Check Point’s flagship annual research publication, the report serves as a reference point...
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard
Google Cloud Platform (GCP) Cloud Monitoring Cross-Tenant BigQuery Leak with Custom Dashboard Tenable Research has identified and responsibly disclosed a data exfiltration vulnerability in Google Cloud Monitoring. This flaw allowed an attacker to leak sensitive data from a victim's BigQuery datasets by abusing the Observability Analytics widget in custom dashboards.Cloud Monitoring dashboards are executed automatically when browsing, and the...
Multiple Critical SolarWinds Web Help Desk Vulnerabilities: CVE-2025-40551, CVE-2025-40552, CVE-2025-40553, CVE-2025-40554
OverviewOn January 28, 2026, SolarWinds published an advisory for multiple new vulnerabilities affecting their Web Help Desk product. Web Help Desk is an IT help desk ticketing and asset management software solution. Of the six new CVEs disclosed in the advisory, four are critical, and allow a remote attacker to either achieve unauthenticated remote code execution (RCE) or bypass...
SmarterTools SmarterMail RCE
What is the Vulnerability? An actively targeted vulnerability has been identified in SmarterTools SmarterMail, tracked as CVE-2025-52691, with a CVSS score of 10.0 (Critical). The flaw allows unauthenticated attackers to upload arbitrary files to any location on the mail server, potentially resulting in remote code execution...
Trusted, Signed, Still Malicious. Exploiting Custom Email Text to Bypass Security Controls
By: Kahng An, Intelligence TeamA recent series of phone scam emails has been able to bypass traditional email security measures by placing malicious messages within document names, online meeting descriptions, or account name fields. These emails redirect otherwise legitimate business emails to potential victims, and are particularly notable for embedding phone scams and other malicious content while still retaining...
Phishing at Cloud Scale: How AWS is Abused for Credential Theft
Threat actors are abusing web services from Amazon like Simple Storage Service (S3) buckets, Amazon Simple Email Service (SES), and Amazon Web Service (AWS) Amplify to launch credential phishing attacks due to their trusted infrastructure, scalability, and ease of abuse. AWS offers threat actors a cloak of legitimacy, bypassing many traditional email based security controls like Secure Email Gateways...
How Elastic Support uses AI to deliver faster, expert-verified solutions
We use AI and RAG to accelerate answers — not replace experts. Every response is reviewed, validated, and refined by engineers to ensure accurate, high-quality, expert-verified solutions, never automated output. - Read more
[R1] Tenable Network Monitor Version 6.5.3 Fixes Multiple Vulnerabilities
Tenable Network Monitor Version 6.5.3 Fixes Multiple Vulnerabilities Arnie Cabral Tue, 01/27/2026 - 14:02
Nessus Network Monitor leverages third-party software to help provide underlying functionality. Several of the third-party components (libxml2, libxslt, expat, c-ares, curl, sqlite) were found to contain vulnerabilities, and updated versions have been made available by the providers. Out of caution and in line with best...
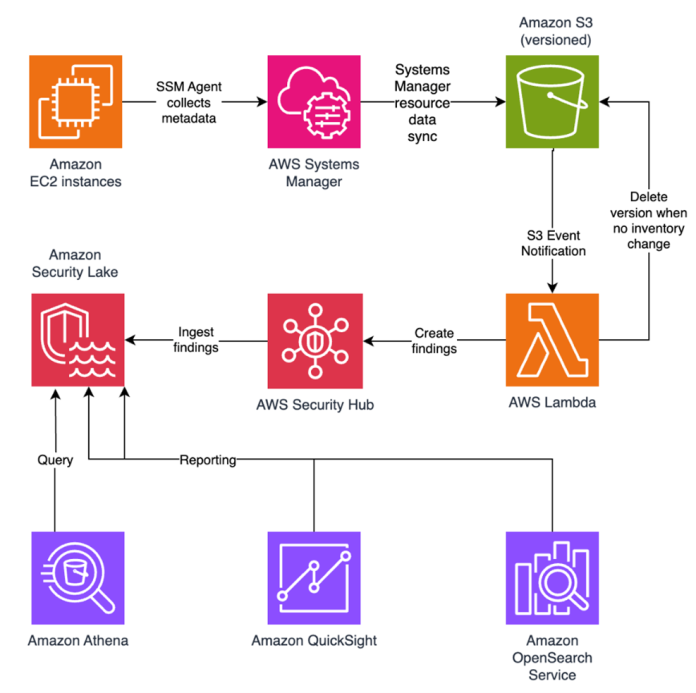
File integrity monitoring with AWS Systems Manager and Amazon Security Lake
Customers need solutions to track inventory data such as files and software across Amazon Elastic Compute Cloud (Amazon EC2) instances, detect unauthorized changes, and integrate alerts into their existing security workflows. In this blog post, I walk you through a highly scalable serverless file integrity monitoring solution. It uses AWS Systems Manager Inventory to collect file metadata...