Ongoing Iran Conflict: What You Need to Know
Recorded Future's Insikt Group® is actively monitoring the rapidly evolving situation following coordinated US-Israeli strikes against Iran and the death of Supreme Leader Ali Khamenei. This analysis serves as a continuously updated compilation of the threat actors, tactics, and infrastructure likely to be involved in Iranian cyber retaliation — both from state-sponsored operators and aligned hacktivist groups -...
OpenClaw 0-Click Vulnerability Allows Malicious Websites to Hijack Developer AI Agents
A critical zero-interaction vulnerability in OpenClaw, one of the fastest-growing open-source AI agent frameworks in history, has been discovered by Oasis Security researchers, allowing any malicious website to silently seize full control of a developer’s AI agent without requiring plugins, extensions, or any user action. OpenClaw, a self-hosted AI agent formerly known as Clawdbot and MoltBot, rocketed to over...
CVE-2025-71147 KEYS: trusted: Fix a memory leak in tpm2_load_cmd
Information published. - Read more
Security hole could let hackers take over Juniper Networks PTX core routers
Network admins with Juniper PTX series routers in their environments are being warned to patch immediately, because a newly-discovered critical vulnerability could lead to an unauthenticated threat actor running code with root privileges. The hole is “especially dangerous, because these devices often sit in the middle of the network, not on the fringes,” said Piyush...
‘Silent’ Google API key change exposed Gemini AI data
Google Cloud API keys, normally used as simple billing identifiers for APIs such as Maps or YouTube, could be scraped from websites to give access to private Gemini AI project data, researchers from Truffle Security recently discovered. According to a Common Crawl scan of websites carried out by the company in November, there were 2,863...
Metasploit Wrap-Up 02/27/2026
No Prob-ollamaThis release brings some serious firepower with multiple new exploit modules and critical vulnerability support! The standout additions are the Ollama path traversal RCE (CVE-2024-37032), a sophisticated exploit chaining arbitrary file writes into unauthenticated root RCE, and the Grandstream GXP1600 stack overflow (CVE-2026-2329), which targets VoIP devices with accompanying credential harvesting and SIP interception post-modules. The BeyondTrust PRA/RS module...
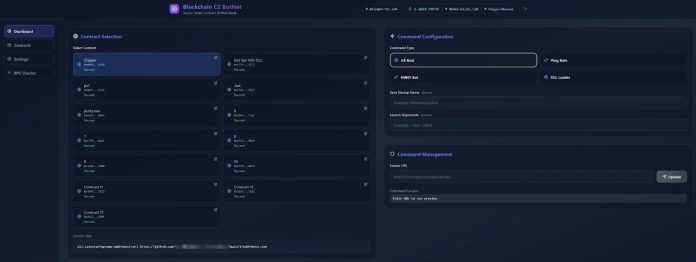
Researchers Uncover Aeternum C2 Infrastructure with Advanced Persistence and Network Evasion Features
For years, taking down a botnet meant finding its command-and-control (C2) server, seizing the domain, and watching the network go dark. Law enforcement used this method to dismantle major operations like Emotet, TrickBot, and QakBot. A newly discovered botnet loader called Aeternum C2 has been built specifically to close that door, storing all of its instructions not on...
5 Nations Alert: Critical Cisco Bug Used in Global Espionage Campaign
Hackers exploited a critical Cisco SD-WAN flaw, prompting a rare joint warning from the US, UK, Australia, Canada, and New Zealand.
The post 5 Nations Alert: Critical Cisco Bug Used in Global Espionage Campaign appeared first on TechRepublic. - Read more
CVE-2026-21518 GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability
Download links fixed - Read more