Unlocking business resilience with full-stack observability in hybrid IT environments
Full-stack observability helps Gulf IT leaders accelerate ROI, strengthen resilience, and advance digital maturity. Learn how to use AI-driven insights and automation to align...
University of Pennsylvania – 623,750 breached accounts
In October 2025, the University of Pennsylvania was the victim of a data breach followed by a ransom demand, largely affecting its donor database....
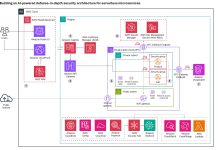
Building an AI-powered defense-in-depth security architecture for serverless microservices
Enterprise customers face an unprecedented security landscape where sophisticated cyber threats use artificial intelligence to identify vulnerabilities, automate attacks, and evade detection...
Fake CAPTCHA Scam Tricks Windows Users Into Installing Malware
A fake CAPTCHA scam is tricking Windows users into running PowerShell commands that install StealC malware and steal passwords, crypto wallets, and more.
The post...
16th February – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 16th February, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
Dutch telecom provider...
Vulnerabilities in Password Managers Allow Hackers to View and Change Passwords
Security researchers have challenged end-to-end encryption claims from popular commercial password managers - Read more
Nanobot Unauthenticated WhatsApp Session Hijack via WebSocket Bridge
Nanobot Unauthenticated WhatsApp Session Hijack via WebSocket Bridge Tenable Research has identified and responsibly disclosed a vulnerability to Nanobot.The nanobot WhatsApp bridge server (`bridge/src/server.ts`)...
Gogs Cross-Repository Comment Deletion via DeleteComment
Gogs Cross-Repository Comment Deletion via DeleteComment Tenable Research has identified and responsibly disclosed an Insecure Direct Object References (IDOR) vulnerability to Gogs. The POST...
APOIA.se – 450,764 breached accounts
In December 2025, a database of the Brazilian crowdfunding platform APOIA.se was posted to an online forum. In January 2026, the company confirmed it...
Making sense of AI’s role in cyber security
Cyber security companies have jumped on the AI bandwagon. We look at where artificial intelligence is a useful add-on and where it poses potential...